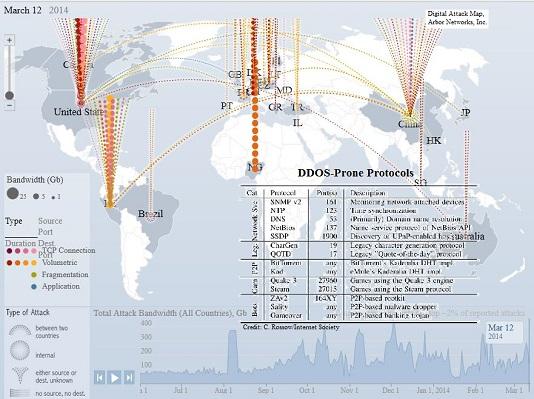
A new set of attack toolkits has drastically changed the balance of power between Websites trying to protect themselves from distributed denial of service attacks, and those using them for extortion, sabotage or revenge. The toolkits make it far simpler to exploit weaknesses in the Network Time Protocol (NTP) – a core function of the Internet that synchronizes the clocks of net-connected servers to within tens of milliseconds, preventing delays by giving all the servers touching a stream of data packets the same deadline for their delivery. Toolkits making it simpler to launch attacks, using a technique called NTP Amplification, were largely responsible for a spike of371 percent in the number of NTP amplification attacks between January and February of this year, according to a March 12 alert from security firm Prolexic. NTP attacks are notoriously large, but recent attacks literally broke the record. A Feb. 13 NTP amplification attack peaked at more than 400Gbit/sec (more than 25 percent larger than the largest DDOS attack ever recorded) on European anti-spam vendor Spamhaus, which peaked at 300Gbit/sec. The Feb. 13 attack could have been launched by "a single server running on a network that allowed source IP address spoofing to initiate the requests," according to CloudFlare CEO Matthew Prince, which reported the attack against one of the sites hosted on its cloud platform. The largest attacks detected so far this year by Prolexic or its parent company, content-delivery network provider Akamai Technologies, Inc., have all been NTP amplification attacks, according to a statement from Stuart Scholly, senior vice president and GM of security at Akamai. NTP amplification attacks aren't rocket science, but a new set of toolkits makes creating them far simpler for a much wider population of potential attackers without the skill to do it on their own. That shifts the risk-management equation by a large step in favor of attackers. "With the current batch of NTP amplification attack toolkits, malicious actors could launch 100 Gbps attacks – or larger – by leveraging just a few vulnerable NTP servers," according to the Prolexic alert. US-CERT advised NTP server owners to upgrade to version 4.2.7 of the NTP software, which disables the monlist feature exploited in the attacks, but there are thousands of vulnerable servers still online. The February attack on CloudFlare involved more than 4,000 vulnerable NTP servers, according to Prince. After publishing a list of the servers involved in the attack, CloudFlare tracked a reduction of 75 percent in the number of NTP servers vulnerable to that particular exploit. The site OpenNTPProject.org, which was set up to allow NTP server owners to test their systems, Tweeted Feb. 14 that it had seen the number of vulnerable servers drop from 490,000 to 349,000 during just the previous week. NTP is not the only service vulnerable to amplification, however. A total of 14 UDP-based Internet protocols are vulnerable to being used as engines of DDOS attacks, six of which could act as amplifiers that increase the volume of those attacks by several orders of magnitude, according to an analysis titled Amplification Hell published for The Internet Society's Network and Distributed System Security (NDSS) Symposium Feb. 23-26 in San Diego, Calif. There are ways to mitigate the attacks or filter bogus traffic, but few administrators seem to be aware of them and fewer still even seem wary of the potential of vulnerable protocols to amplify DDOS attacks to levels for which few organizations are prepared, Rossow found. There are millions of servers online that could act as platforms for the six amplifier protocols, warned Christian Rossow, the University of Amsterdam researcher who wrote the paper. "This [research] shows that there is an urgent need to harden the protocols/implementations at least of the most severely affected services, such as DNS, NTP, SSDP or Kad," Rossow concluded. "Network administrators should be prepared for DDOS attacks that are at least a magnitude worse from what we have observed so far." The real-time attack map maintained by Arbor Networks shows intense attacks in the U.S., China, Peru and Europe – at bandwidths that were almost always below 100Gbit/sec until mid-August, 2013, and have only rarely dipped below that mark since then. Image: Arbor Networks/C. Rossow/Internet Society