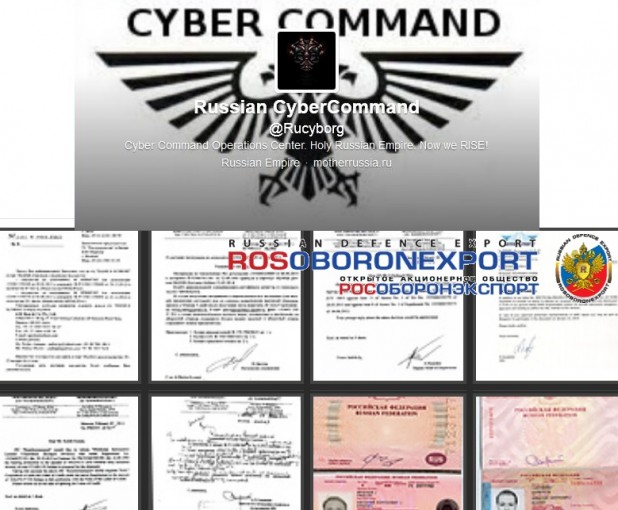
 A group of Russian hacktivists has taken a page from the playbook written by WikiLeaks and Edward Snowden, protesting aggressive political policies by releasing 1,000 documents allegedly stolen from the agency that oversees the export of Russian weapons to foreign countries. The group, which calls itself the Russian Cyber Command, uploaded about 500MB of documents allegedly stolen from the servers of the Rosoboronexport State Corporation to protest "Putin's Empire" and the "Russian Government['s] delusional attempts to start WWIII," according to a March 6 story on SoftPedia. The group posted a preview of the documents on Imgur and uploaded the files to BayFiles (caution: compressed .rar files, not scanned for malware), a hosting company and repository created by founders of The Pirate Bay, according to a statement from the group posted on its site CyberGuerrila.org. The documents appear to be related to deals with companies, including Indian aerospace company Hindustan Aeronautics Ltd., complete with travel plans and details about the passports of Russian delegates, and digital images of the passports themselves, according to a March 6 story in CyberWarNews.info. The documents, compressed in a .rar file, are also thoroughly infected with an impressive list of Trojans, viruses and other malware, according to a VirusTotal scan run by CyberWarNews. The group has been posting updates (in Russian) at its Twitter account @Rucyborg, which has attracted kudos and support from accounts associated with the more U.S./U.K-centered hacktivist group Anonymous. In its statement, the group claimed to have cracked Rosoboronexport using malware embedded in an email sent to the CEO of Rosoboronexport from servers belonging to India's embassy in Moscow, which it penetrated to give itself a safe-seeming origin point for the email that formed the point of its attack. The group, which referred to itself as "free computer renegades and outlaws from IT Security," said the breach and release of the documents was part of an effort to "initiate a true domestic CyberWar on Russian Military Enterprises and eventually we shall deliver critical infrastructure companies on which Russian Putin’s Empire stands on." The outrage and attacks appear to be a response to Russia's attack on the Crimean peninsula in Ukraine, following a popular uprising that overthrew Russian-favoring Ukranian President Viktor Yanukovych, who asked for Russian military help to suppress "extremists" and "armed national radicals" before fleeing the country himself, according to a briefing to the UN Security Council given March 3 by Russian UN Ambassador Vitaly Churkin. A March 2 analysis from the Georgetown University Security Studies Review – written by Masters candidate Jason Rivera, who is an active-duty officer in the U.S. Army Cyber Command – warned that the Russian military response was likely to include both "kinetic" and digital attacks, including DDoS attacks against Ukranian government or military institutions. Parts of Ukraine's telecommunications system were offline and the mobile telephones of many Ukrainian parliament members were out of service following digital attacks from Russian-controlled areas of the Crimean Peninsula earlier this week, according to a March 3 announcement from Valentyn Nalivaichenko, the head of Ukraine's SBU security service. "The security services are now seeking to restore at least the security of communications," Reuters quoted him as saying during a press conference. "All state information security systems were unprepared for such a brazen violation of the law." The Russian Cyber Command statement promised more documents were to come from hacks of other Russian defense-related companies including Sukhoi, Oboronprom, Gazflot and Rusal. Image: Rosoboronexport , via Russian Cyber Command
A group of Russian hacktivists has taken a page from the playbook written by WikiLeaks and Edward Snowden, protesting aggressive political policies by releasing 1,000 documents allegedly stolen from the agency that oversees the export of Russian weapons to foreign countries. The group, which calls itself the Russian Cyber Command, uploaded about 500MB of documents allegedly stolen from the servers of the Rosoboronexport State Corporation to protest "Putin's Empire" and the "Russian Government['s] delusional attempts to start WWIII," according to a March 6 story on SoftPedia. The group posted a preview of the documents on Imgur and uploaded the files to BayFiles (caution: compressed .rar files, not scanned for malware), a hosting company and repository created by founders of The Pirate Bay, according to a statement from the group posted on its site CyberGuerrila.org. The documents appear to be related to deals with companies, including Indian aerospace company Hindustan Aeronautics Ltd., complete with travel plans and details about the passports of Russian delegates, and digital images of the passports themselves, according to a March 6 story in CyberWarNews.info. The documents, compressed in a .rar file, are also thoroughly infected with an impressive list of Trojans, viruses and other malware, according to a VirusTotal scan run by CyberWarNews. The group has been posting updates (in Russian) at its Twitter account @Rucyborg, which has attracted kudos and support from accounts associated with the more U.S./U.K-centered hacktivist group Anonymous. In its statement, the group claimed to have cracked Rosoboronexport using malware embedded in an email sent to the CEO of Rosoboronexport from servers belonging to India's embassy in Moscow, which it penetrated to give itself a safe-seeming origin point for the email that formed the point of its attack. The group, which referred to itself as "free computer renegades and outlaws from IT Security," said the breach and release of the documents was part of an effort to "initiate a true domestic CyberWar on Russian Military Enterprises and eventually we shall deliver critical infrastructure companies on which Russian Putin’s Empire stands on." The outrage and attacks appear to be a response to Russia's attack on the Crimean peninsula in Ukraine, following a popular uprising that overthrew Russian-favoring Ukranian President Viktor Yanukovych, who asked for Russian military help to suppress "extremists" and "armed national radicals" before fleeing the country himself, according to a briefing to the UN Security Council given March 3 by Russian UN Ambassador Vitaly Churkin. A March 2 analysis from the Georgetown University Security Studies Review – written by Masters candidate Jason Rivera, who is an active-duty officer in the U.S. Army Cyber Command – warned that the Russian military response was likely to include both "kinetic" and digital attacks, including DDoS attacks against Ukranian government or military institutions. Parts of Ukraine's telecommunications system were offline and the mobile telephones of many Ukrainian parliament members were out of service following digital attacks from Russian-controlled areas of the Crimean Peninsula earlier this week, according to a March 3 announcement from Valentyn Nalivaichenko, the head of Ukraine's SBU security service. "The security services are now seeking to restore at least the security of communications," Reuters quoted him as saying during a press conference. "All state information security systems were unprepared for such a brazen violation of the law." The Russian Cyber Command statement promised more documents were to come from hacks of other Russian defense-related companies including Sukhoi, Oboronprom, Gazflot and Rusal. Image: Rosoboronexport , via Russian Cyber Command Hack of Russian Defense Firm Called 'Cyberwar'
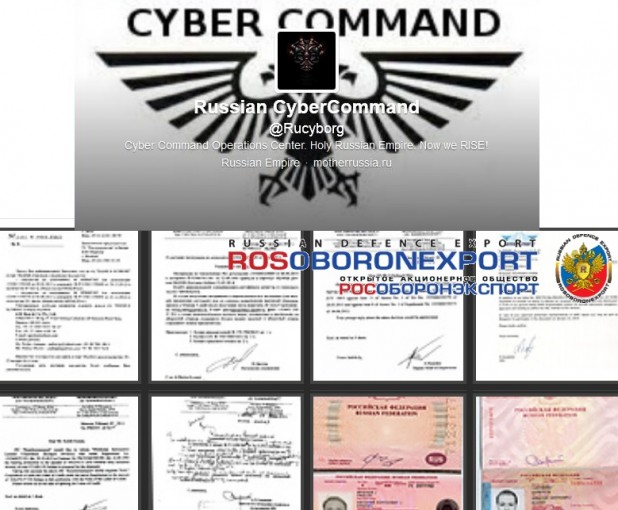 A group of Russian hacktivists has taken a page from the playbook written by WikiLeaks and Edward Snowden, protesting aggressive political policies by releasing 1,000 documents allegedly stolen from the agency that oversees the export of Russian weapons to foreign countries. The group, which calls itself the Russian Cyber Command, uploaded about 500MB of documents allegedly stolen from the servers of the Rosoboronexport State Corporation to protest "Putin's Empire" and the "Russian Government['s] delusional attempts to start WWIII," according to a March 6 story on SoftPedia. The group posted a preview of the documents on Imgur and uploaded the files to BayFiles (caution: compressed .rar files, not scanned for malware), a hosting company and repository created by founders of The Pirate Bay, according to a statement from the group posted on its site CyberGuerrila.org. The documents appear to be related to deals with companies, including Indian aerospace company Hindustan Aeronautics Ltd., complete with travel plans and details about the passports of Russian delegates, and digital images of the passports themselves, according to a March 6 story in CyberWarNews.info. The documents, compressed in a .rar file, are also thoroughly infected with an impressive list of Trojans, viruses and other malware, according to a VirusTotal scan run by CyberWarNews. The group has been posting updates (in Russian) at its Twitter account @Rucyborg, which has attracted kudos and support from accounts associated with the more U.S./U.K-centered hacktivist group Anonymous. In its statement, the group claimed to have cracked Rosoboronexport using malware embedded in an email sent to the CEO of Rosoboronexport from servers belonging to India's embassy in Moscow, which it penetrated to give itself a safe-seeming origin point for the email that formed the point of its attack. The group, which referred to itself as "free computer renegades and outlaws from IT Security," said the breach and release of the documents was part of an effort to "initiate a true domestic CyberWar on Russian Military Enterprises and eventually we shall deliver critical infrastructure companies on which Russian Putin’s Empire stands on." The outrage and attacks appear to be a response to Russia's attack on the Crimean peninsula in Ukraine, following a popular uprising that overthrew Russian-favoring Ukranian President Viktor Yanukovych, who asked for Russian military help to suppress "extremists" and "armed national radicals" before fleeing the country himself, according to a briefing to the UN Security Council given March 3 by Russian UN Ambassador Vitaly Churkin. A March 2 analysis from the Georgetown University Security Studies Review – written by Masters candidate Jason Rivera, who is an active-duty officer in the U.S. Army Cyber Command – warned that the Russian military response was likely to include both "kinetic" and digital attacks, including DDoS attacks against Ukranian government or military institutions. Parts of Ukraine's telecommunications system were offline and the mobile telephones of many Ukrainian parliament members were out of service following digital attacks from Russian-controlled areas of the Crimean Peninsula earlier this week, according to a March 3 announcement from Valentyn Nalivaichenko, the head of Ukraine's SBU security service. "The security services are now seeking to restore at least the security of communications," Reuters quoted him as saying during a press conference. "All state information security systems were unprepared for such a brazen violation of the law." The Russian Cyber Command statement promised more documents were to come from hacks of other Russian defense-related companies including Sukhoi, Oboronprom, Gazflot and Rusal. Image: Rosoboronexport , via Russian Cyber Command
A group of Russian hacktivists has taken a page from the playbook written by WikiLeaks and Edward Snowden, protesting aggressive political policies by releasing 1,000 documents allegedly stolen from the agency that oversees the export of Russian weapons to foreign countries. The group, which calls itself the Russian Cyber Command, uploaded about 500MB of documents allegedly stolen from the servers of the Rosoboronexport State Corporation to protest "Putin's Empire" and the "Russian Government['s] delusional attempts to start WWIII," according to a March 6 story on SoftPedia. The group posted a preview of the documents on Imgur and uploaded the files to BayFiles (caution: compressed .rar files, not scanned for malware), a hosting company and repository created by founders of The Pirate Bay, according to a statement from the group posted on its site CyberGuerrila.org. The documents appear to be related to deals with companies, including Indian aerospace company Hindustan Aeronautics Ltd., complete with travel plans and details about the passports of Russian delegates, and digital images of the passports themselves, according to a March 6 story in CyberWarNews.info. The documents, compressed in a .rar file, are also thoroughly infected with an impressive list of Trojans, viruses and other malware, according to a VirusTotal scan run by CyberWarNews. The group has been posting updates (in Russian) at its Twitter account @Rucyborg, which has attracted kudos and support from accounts associated with the more U.S./U.K-centered hacktivist group Anonymous. In its statement, the group claimed to have cracked Rosoboronexport using malware embedded in an email sent to the CEO of Rosoboronexport from servers belonging to India's embassy in Moscow, which it penetrated to give itself a safe-seeming origin point for the email that formed the point of its attack. The group, which referred to itself as "free computer renegades and outlaws from IT Security," said the breach and release of the documents was part of an effort to "initiate a true domestic CyberWar on Russian Military Enterprises and eventually we shall deliver critical infrastructure companies on which Russian Putin’s Empire stands on." The outrage and attacks appear to be a response to Russia's attack on the Crimean peninsula in Ukraine, following a popular uprising that overthrew Russian-favoring Ukranian President Viktor Yanukovych, who asked for Russian military help to suppress "extremists" and "armed national radicals" before fleeing the country himself, according to a briefing to the UN Security Council given March 3 by Russian UN Ambassador Vitaly Churkin. A March 2 analysis from the Georgetown University Security Studies Review – written by Masters candidate Jason Rivera, who is an active-duty officer in the U.S. Army Cyber Command – warned that the Russian military response was likely to include both "kinetic" and digital attacks, including DDoS attacks against Ukranian government or military institutions. Parts of Ukraine's telecommunications system were offline and the mobile telephones of many Ukrainian parliament members were out of service following digital attacks from Russian-controlled areas of the Crimean Peninsula earlier this week, according to a March 3 announcement from Valentyn Nalivaichenko, the head of Ukraine's SBU security service. "The security services are now seeking to restore at least the security of communications," Reuters quoted him as saying during a press conference. "All state information security systems were unprepared for such a brazen violation of the law." The Russian Cyber Command statement promised more documents were to come from hacks of other Russian defense-related companies including Sukhoi, Oboronprom, Gazflot and Rusal. Image: Rosoboronexport , via Russian Cyber Command