[caption id="attachment_17482" align="aligncenter" width="571"]
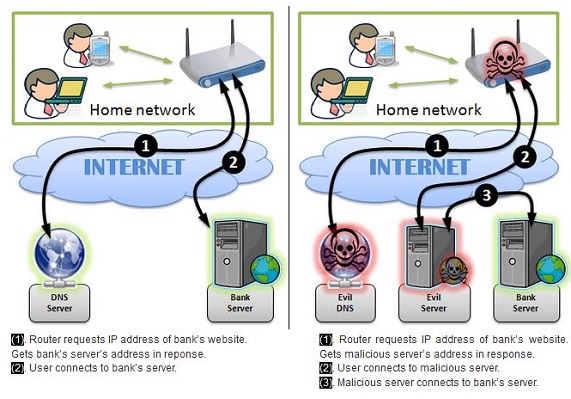
Flaws in home routers let Polish hackers rob banks using man-in-the-middle attacks.[/caption] The remote-access management flaw that allowed TheMoon worm to thrive on Linksys routers is far from the only vulnerability in that particular brand of hardware, though it might be simpler to call all home-based wireless routers gaping holes of insecurity than to list all the flaws in those of just one vendor. Many of the same Linksys routers with flaws that make them vulnerable to infection by TheMoon ship with
other doors and windows open. Chief among them is a bug that would allow a remote user to
access the administrative console of a Linksys router without logging in first, using port 8083, which is left open on many Linksys models. Vulnerable machines include the Linksys EA2700, EA3500, E4200 or EA4500, according to security researcher Kyle Lovett and SANS Institute Internet Storm Center (ICS)'s Matt Claunch, who reported it to Linksys in July 2013. Routers vulnerable to TheMoon include the E4200, E3200, E3000, E2500, E2100L, E2000, E1550, E1500, E1200, E1000 and E900,
added the ICS, which first discovered the infestation. An even longer list of Linksys (and Cisco and Netgear) routers were identified in January as having a
backdoor built into the original versions of their firmware in 2005 and never taken out. Serious as those flaws are, they don't compare to the list of vulnerabilities resulting from an impossibly complex mesh of sophisticated network services that make nearly every router aimed at homes or small offices an easy target for attack, according to network-security penetration- and testing services. Wireless routers (especially home routers owned by technically challenged consumers) are riddled with security holes stemming from design goals that emphasize
usability over security, which often puts consumers at risk from malware or attacks on devices they don't know how to monitor, but through which flow all their personal and financial information via links to online banking, entertainment, credit cards and even direct connections to their work networks, according to a
condemnation of the Home Network Administration Protocol (HNAP) from Tenable Network Security. Universal Plug and Play (UPnP), another protocol that is ubiquitous in home networking devices, is also
riddled with security problems, according to Paul Asadoorian, the Tenable researcher who panned HNAP and has written a series of papers on
hacking embedded devices, especially wireless home routers. It doesn’t take much actual hacking to take over most home routers, according to another security firm, Independent Security Evaluators (ISE), which discovered 55 new and undisclosed vulnerabilities in home routers during the course of research for one report that concluded few, if any home routers could be secured at all. In addition to the HNAP vulnerability in both Linksys and D-Link routers, which could allow attackers to take remote control of home networks, wireless routers are vulnerable to so many potential types of attacks across both WLAN and WAN interfaces that they make millions of consumers easy targets for almost any type of cyberattack, according to an
April 2013 ISE study. A 2010 study from
SourceSec Security Research also found that nearly all home routers are easily vulnerable to attacks using UPnP, iFrame, authentication bypass, domain-name hijacking, Java, DHCP, invalid XML/HTML tags, CSRF, default WEP keys, session hijacking and other techniques. A January 2013
study from Rapid7 found 40 million to 50 million network-enabled devices, including nearly all home routers, were vulnerable to exploits using UPnP. The problem isn't weaknesses in each of those protocols or availability of exploits using specific techniques, according to ISE. It's that small-office, home office (SOHO) routers are designed to be easy for the non-technical to use, but rich in features that depend on often complex networking protocols. Most ship with default admin credentials that are easy to guess and sometimes impossible to delete after they're changed, or a long list of extraneous, often complex, services built into most home routers and the virtual impossibility of either shutting them down or securing them. In addition to services related to switching or routing, every one of the routers tested had at least one service configured to support network attached storage (NAS), including FTP, Short Message Block (SMB), NetBIOS, UPnP Media and HTTP that were also open to attack. Others included "special" services such as ACSD, which ran in TRENDnet and Asus routers to help determine the best radio frequency on which to broadcast, and which could be exploited to allow attackers to take over the router completely. Many services can't be shut down by the administrator. When potentially vulnerable services could be shut down, attacks using other services, or inadequate security built into the routers themselves, would allow attackers to simply turn the banned services back on. Sixty percent of the routers tested allowed users to log in to the administrative console using passwords sent wirelessly via HTTP – clear text broadcast over the air. Only 40 percent of the routers tested provided HTTPS connections and only 20 percent used it by default. That would be fine if the routers and their wireless signals were available only in secure places, but SOHO routers are used in coffee shops, libraries, small businesses, and other public places, and bleed through apartment walls or between close-packed houses: situations in which strangers could easily listen in. The ISE report concluded:
"Once compromised, any router—SOHO or otherwise—may be used by an adversary to secure a man-in-the-middle position for launching more sophisticated attacks against all users in the router's domain. This includes sniffing and rerouting all network traffic, poisoning DNS resolvers, performing denial of service attacks, or impersonating servers. Worse still, is that these routers are also firewalls, and often represent the first (and last) line of defense for protecting the local network. Once compromised, the adversary has unfettered access to exploit the vulnerabilities of local area hosts that would be otherwise unreachable if the router were enforcing firewall rules as intended."
Of the small-office, home-office routers evaluated, every one could be compromised with relative ease by hijacking DNS connections, exploiting HTTPS flaws, weaknesses in Universal Plug and Play services, cross-site-scripting attacks, file-traversal and source-code vulnerabilities, weaknesses in WiFi Protected Setup (WPS), buffer overflows or simply bypassing authentication requirements. Even the SCSD service that allows routers to choose the most efficient radio channel for WLAN connections can be exploited to give attackers full control over the router, according to the ISE report. Last April, only half an hour of testing the security on the Linksys EA2700 Network Manager N600 WiFi Wireless-N Router led San Jose security researcher and
Black Hat conference presenter Phil Purviance to decide that
"any network with an EA2700 router on it is an insecure network." Attackers could take control using
cross-site request forgeries (CSRF), cross-site scripting (XSS) flaws on CGI pages, file-path traversals that give access to password and configuration files with no login or POST requests, in order to turn remote management on and reset the admin password to "password." They could also add a "/" to any page in the administrative panel to see the raw web-application-level source code underlying all the router's configuration and administration, Purviance wrote. (Full results
here.) "This is just STUPID," Purviance wrote in the blog entry titled
Don't Use Linksys Routers. "I don't know whether to laugh or cry at this because it's essentially the same as putting an unpatched Windows machine directly on the Internet. This is just so sad that I really don't know what else to say about this." The weak security of home routers is so common it's difficult to pin specific hacks or incidents of digital fraud specifically to SOHO routers alone, but there are some common elements that sometimes make it obvious, however. During late 2013 and early 2014, gangs of Polish hackers have robbed thousands of consumers by attacking home routers and changing DNS settings so they point at the attackers' DNS servers rather than legitimate servers. That allows them to intercept traffic primarily for online banking sites and launch man-in-the-middle attacks that are virtually impossible for either the consumer or bank to detect until it's too late,
according to a Feb. 7 IDG News story. While the attacks have been widespread, they haven't been traceable to a single specific flaw in a network service or type of router. Once the DNS configuration of one home router is compromised, the effects propagate to all the users in a local network, whether that be a home or small business, according to CERT Polska's blog describing the problem. While there are some ways to identify an attack in progress, the only real solution is to protect home routers from attack by disabling any kind of remote administrative access to the router, changing default usernames and passwords and updating firmware on routers. CERT Polska doesn't have a firm count of victims, but said thousands of home routers were compromised and as many as 1.2 million devices are vulnerable to similar attacks,
according to an SCMagazine story Feb. 13. CERT Polska did identify DNS vulnerabilities in firmware for some TPLink and DLink routers, but only in a version released after the hijackings were already underway, Przemyslaw Jaroszewski, head of Poland's CERT, told SCMagazine. "There are also recently discovered CSRF vulnerabilities in routers widely used by UPC – one of the largest ISPs in Europe," he said. Neither of those specific weaknesses could have delivered as many victims as Polish police have identified, however. "There are many ways to modify DNS entries in home routers, some of them known for years," Jaroszewski told IDGNews. "It is actually surprising that it's the first time we see it exploited for profit on a mass scale."
Image: CERT Polska 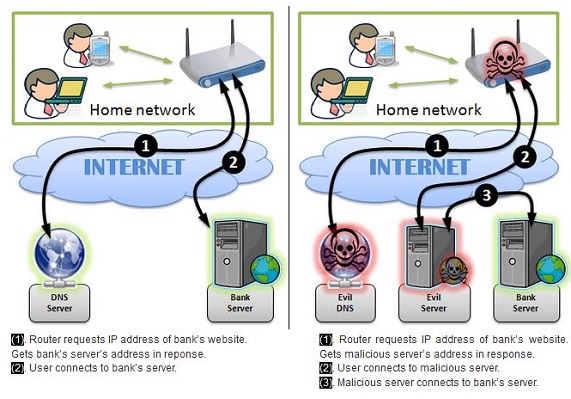 Flaws in home routers let Polish hackers rob banks using man-in-the-middle attacks.[/caption] The remote-access management flaw that allowed TheMoon worm to thrive on Linksys routers is far from the only vulnerability in that particular brand of hardware, though it might be simpler to call all home-based wireless routers gaping holes of insecurity than to list all the flaws in those of just one vendor. Many of the same Linksys routers with flaws that make them vulnerable to infection by TheMoon ship with other doors and windows open. Chief among them is a bug that would allow a remote user to access the administrative console of a Linksys router without logging in first, using port 8083, which is left open on many Linksys models. Vulnerable machines include the Linksys EA2700, EA3500, E4200 or EA4500, according to security researcher Kyle Lovett and SANS Institute Internet Storm Center (ICS)'s Matt Claunch, who reported it to Linksys in July 2013. Routers vulnerable to TheMoon include the E4200, E3200, E3000, E2500, E2100L, E2000, E1550, E1500, E1200, E1000 and E900, added the ICS, which first discovered the infestation. An even longer list of Linksys (and Cisco and Netgear) routers were identified in January as having a backdoor built into the original versions of their firmware in 2005 and never taken out. Serious as those flaws are, they don't compare to the list of vulnerabilities resulting from an impossibly complex mesh of sophisticated network services that make nearly every router aimed at homes or small offices an easy target for attack, according to network-security penetration- and testing services. Wireless routers (especially home routers owned by technically challenged consumers) are riddled with security holes stemming from design goals that emphasize usability over security, which often puts consumers at risk from malware or attacks on devices they don't know how to monitor, but through which flow all their personal and financial information via links to online banking, entertainment, credit cards and even direct connections to their work networks, according to a condemnation of the Home Network Administration Protocol (HNAP) from Tenable Network Security. Universal Plug and Play (UPnP), another protocol that is ubiquitous in home networking devices, is also riddled with security problems, according to Paul Asadoorian, the Tenable researcher who panned HNAP and has written a series of papers on hacking embedded devices, especially wireless home routers. It doesn’t take much actual hacking to take over most home routers, according to another security firm, Independent Security Evaluators (ISE), which discovered 55 new and undisclosed vulnerabilities in home routers during the course of research for one report that concluded few, if any home routers could be secured at all. In addition to the HNAP vulnerability in both Linksys and D-Link routers, which could allow attackers to take remote control of home networks, wireless routers are vulnerable to so many potential types of attacks across both WLAN and WAN interfaces that they make millions of consumers easy targets for almost any type of cyberattack, according to an April 2013 ISE study. A 2010 study from SourceSec Security Research also found that nearly all home routers are easily vulnerable to attacks using UPnP, iFrame, authentication bypass, domain-name hijacking, Java, DHCP, invalid XML/HTML tags, CSRF, default WEP keys, session hijacking and other techniques. A January 2013 study from Rapid7 found 40 million to 50 million network-enabled devices, including nearly all home routers, were vulnerable to exploits using UPnP. The problem isn't weaknesses in each of those protocols or availability of exploits using specific techniques, according to ISE. It's that small-office, home office (SOHO) routers are designed to be easy for the non-technical to use, but rich in features that depend on often complex networking protocols. Most ship with default admin credentials that are easy to guess and sometimes impossible to delete after they're changed, or a long list of extraneous, often complex, services built into most home routers and the virtual impossibility of either shutting them down or securing them. In addition to services related to switching or routing, every one of the routers tested had at least one service configured to support network attached storage (NAS), including FTP, Short Message Block (SMB), NetBIOS, UPnP Media and HTTP that were also open to attack. Others included "special" services such as ACSD, which ran in TRENDnet and Asus routers to help determine the best radio frequency on which to broadcast, and which could be exploited to allow attackers to take over the router completely. Many services can't be shut down by the administrator. When potentially vulnerable services could be shut down, attacks using other services, or inadequate security built into the routers themselves, would allow attackers to simply turn the banned services back on. Sixty percent of the routers tested allowed users to log in to the administrative console using passwords sent wirelessly via HTTP – clear text broadcast over the air. Only 40 percent of the routers tested provided HTTPS connections and only 20 percent used it by default. That would be fine if the routers and their wireless signals were available only in secure places, but SOHO routers are used in coffee shops, libraries, small businesses, and other public places, and bleed through apartment walls or between close-packed houses: situations in which strangers could easily listen in. The ISE report concluded:
Flaws in home routers let Polish hackers rob banks using man-in-the-middle attacks.[/caption] The remote-access management flaw that allowed TheMoon worm to thrive on Linksys routers is far from the only vulnerability in that particular brand of hardware, though it might be simpler to call all home-based wireless routers gaping holes of insecurity than to list all the flaws in those of just one vendor. Many of the same Linksys routers with flaws that make them vulnerable to infection by TheMoon ship with other doors and windows open. Chief among them is a bug that would allow a remote user to access the administrative console of a Linksys router without logging in first, using port 8083, which is left open on many Linksys models. Vulnerable machines include the Linksys EA2700, EA3500, E4200 or EA4500, according to security researcher Kyle Lovett and SANS Institute Internet Storm Center (ICS)'s Matt Claunch, who reported it to Linksys in July 2013. Routers vulnerable to TheMoon include the E4200, E3200, E3000, E2500, E2100L, E2000, E1550, E1500, E1200, E1000 and E900, added the ICS, which first discovered the infestation. An even longer list of Linksys (and Cisco and Netgear) routers were identified in January as having a backdoor built into the original versions of their firmware in 2005 and never taken out. Serious as those flaws are, they don't compare to the list of vulnerabilities resulting from an impossibly complex mesh of sophisticated network services that make nearly every router aimed at homes or small offices an easy target for attack, according to network-security penetration- and testing services. Wireless routers (especially home routers owned by technically challenged consumers) are riddled with security holes stemming from design goals that emphasize usability over security, which often puts consumers at risk from malware or attacks on devices they don't know how to monitor, but through which flow all their personal and financial information via links to online banking, entertainment, credit cards and even direct connections to their work networks, according to a condemnation of the Home Network Administration Protocol (HNAP) from Tenable Network Security. Universal Plug and Play (UPnP), another protocol that is ubiquitous in home networking devices, is also riddled with security problems, according to Paul Asadoorian, the Tenable researcher who panned HNAP and has written a series of papers on hacking embedded devices, especially wireless home routers. It doesn’t take much actual hacking to take over most home routers, according to another security firm, Independent Security Evaluators (ISE), which discovered 55 new and undisclosed vulnerabilities in home routers during the course of research for one report that concluded few, if any home routers could be secured at all. In addition to the HNAP vulnerability in both Linksys and D-Link routers, which could allow attackers to take remote control of home networks, wireless routers are vulnerable to so many potential types of attacks across both WLAN and WAN interfaces that they make millions of consumers easy targets for almost any type of cyberattack, according to an April 2013 ISE study. A 2010 study from SourceSec Security Research also found that nearly all home routers are easily vulnerable to attacks using UPnP, iFrame, authentication bypass, domain-name hijacking, Java, DHCP, invalid XML/HTML tags, CSRF, default WEP keys, session hijacking and other techniques. A January 2013 study from Rapid7 found 40 million to 50 million network-enabled devices, including nearly all home routers, were vulnerable to exploits using UPnP. The problem isn't weaknesses in each of those protocols or availability of exploits using specific techniques, according to ISE. It's that small-office, home office (SOHO) routers are designed to be easy for the non-technical to use, but rich in features that depend on often complex networking protocols. Most ship with default admin credentials that are easy to guess and sometimes impossible to delete after they're changed, or a long list of extraneous, often complex, services built into most home routers and the virtual impossibility of either shutting them down or securing them. In addition to services related to switching or routing, every one of the routers tested had at least one service configured to support network attached storage (NAS), including FTP, Short Message Block (SMB), NetBIOS, UPnP Media and HTTP that were also open to attack. Others included "special" services such as ACSD, which ran in TRENDnet and Asus routers to help determine the best radio frequency on which to broadcast, and which could be exploited to allow attackers to take over the router completely. Many services can't be shut down by the administrator. When potentially vulnerable services could be shut down, attacks using other services, or inadequate security built into the routers themselves, would allow attackers to simply turn the banned services back on. Sixty percent of the routers tested allowed users to log in to the administrative console using passwords sent wirelessly via HTTP – clear text broadcast over the air. Only 40 percent of the routers tested provided HTTPS connections and only 20 percent used it by default. That would be fine if the routers and their wireless signals were available only in secure places, but SOHO routers are used in coffee shops, libraries, small businesses, and other public places, and bleed through apartment walls or between close-packed houses: situations in which strangers could easily listen in. The ISE report concluded: