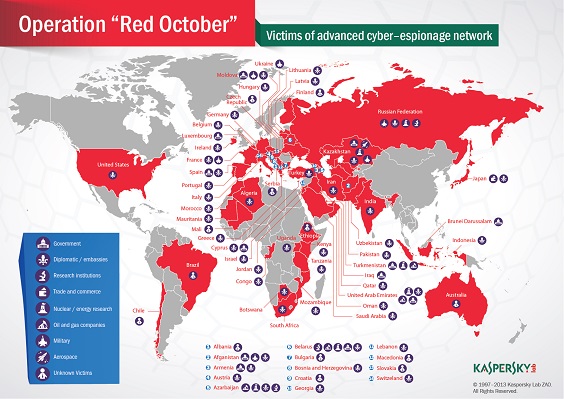
 'Red October' attack may have touched off global online arms race.[/caption] On the same day the Obama Administration revealed its pick for the new head of the National Security Agency (NSA), Russian officials announced they will launch a new military unit devoted to keeping digital attacks from crippling the Russian military. The new cyberdefense unit, which is due to go into operation by 2017, will be created "to defend Russian armed forces' critical infrastructure from computer attacks," according to Maj. Gen. Yuri Kuznetsov, who was quoted in the state-backed RIA Novosti news agency. It may or may not be coincidence that Kuznetsov's announcement came on the same day the White House leaked its plan to appoint U.S. Navy Vice Admiral Michael S. Rogers to take over as head of the NSA and Pentagon's Cyber Command, following the retirement of embattled current NSA director Gen. Keith. B. Alexander. Though Pentagon and White House officials emphasized Rogers' technical and administrative qualifications for the job, Rogers is on record as advocating a "warrior ethos" among military cyber-security crews that would encourage use of military networks and other digital resources as weapons rather than just infrastructure to be maintained. Moscow's Jan. 30 announcement that it would create a defensive cyber-force was not the first time Russian officials have complained about online attacks, or announced plans to beef up defense against them using both the secret police and the military. RIA Novosti reported in April that the Russian Interior Ministry would spend the equivalent of $1.3 million on security to prevent attacks on its computer networks and to link with similar intrusion-prevention systems used by the Russian Federal Security Service (FSB) – the post-Soviet ancestor of the KGB. Russian officials complained at the time that Websites belonging to the office of the President and two houses of the Russian parliament sustained up to 10,000 attacks every day. A more serious reason may be the virus, dubbed "Red October," that was discovered infecting Russian government systems with programming designed to "gather sensitive documents," according to an advisory from Kaspersky Labs, which published a report on the virus Jan. 14, 2013. The virus had been active since at least 2007, was most concentrated in diplomatic and government agencies of various countries, and was spread by malware identified as "Rocra," which carried a variable payload that could include information-stealing modules and Trojans to create backdoors into secure systems. Rocra and Red October are part of a "high-level cyber-espionage campaign has successfully infiltrated computer networks at diplomatic, governmental and scientific research organizations," according to the Kaspersky analysis. Red October's sophistication and effectiveness is nearly as great as that of the "Flame" malware – an attack toolkit even more sophisticated that the Duqu and Stuxnet viruses that were designed to attack nuclear-development facilities in Iran, according to Kaspersky. Flame, which is believed to have been created by a state-sponsored intelligence agency, "pretty much redefines the notion of cyberwar and cyberespionage," according to a May 2013 Kaspersky analysis. Russian President Vladimir Putin responded to news of the Red October virus by ordering the FSB to create a system designed to identify and prevent cyberattacks, and by proposing a cooperative anti-cybercrime enforcement agreement with China, according to RIA Novosti. Russian military officials announced in August they were creating a special cyber warfare unit that would become active as early as 2014 to prepare for the potential of the Internet to become "a theater of war." "The world is getting ready for a new arms race—this time in cyber weapons," according to a June 26 article by RIA Novosti commentator Konstantin Bogdanov. In the piece, Bogdanov accused U.S. intelligence agencies under Presidential Administration of George W. Bush of having created and launched not only Duqu, Stuxnet and Flame, but of weaponizing the Internet and launching a new arms race in cyberspace. "What was previously considered to be the domain of semi-criminal marginal groups or a cheap way of expressing sociopathy is now attracting the interest of governments, who are considering producing weaponized software on an industrial scale," Bogdanov wrote. The effort is rash, provocative and dangerous, Bogdanov warned, under the heading, "Don't play with matches at a gas station," in which he compared the current state of militarized malware to the period between July 16 1945 and Aug. 6, 1945, "after the United States tested its first nuclear device near Alamagordo [N.M.] but had not yet dropped any nuclear bombs on Japanese cities." Though Russian officials resolutely accuse U.S. agencies of being the main force behind state-sponsored cyberwar and cyber-espionage, Russian agencies have never been shy about online intrusions and have stepped up their activities during the past decade, according to U.S.-based security analysis firm CrowdStrike. In a report summarizing cyber-espionage activity by 50 "cyber threat actors," CrowdStrike noted a sharp increase in attacks from the Russian group nicknamed "Energetic Bear." During the past two years, Russian groups have used an increasingly sophisticated menu of tools and techniques to penetrate energy companies, defense contractors, technology companies and government agencies in Europe, Asia and the U.S., acquiring information of political or military interest, but also expanding into good old-fashioned industrial espionage. CrowdStrike characterized 34 of the 41 primary "cyberadversaries" it identified in the report as being nation-states. "Observed indicators obtained from monitoring this adversary's activity suggest that Energetic Bear is operating out of Russia, or at least on behalf of Russia-based interests, and it is possible that their operations are carried out with the sponsorship and knowledge of the Russian state," the CrowdStrike report concluded. Image: Kaspersky Labs
'Red October' attack may have touched off global online arms race.[/caption] On the same day the Obama Administration revealed its pick for the new head of the National Security Agency (NSA), Russian officials announced they will launch a new military unit devoted to keeping digital attacks from crippling the Russian military. The new cyberdefense unit, which is due to go into operation by 2017, will be created "to defend Russian armed forces' critical infrastructure from computer attacks," according to Maj. Gen. Yuri Kuznetsov, who was quoted in the state-backed RIA Novosti news agency. It may or may not be coincidence that Kuznetsov's announcement came on the same day the White House leaked its plan to appoint U.S. Navy Vice Admiral Michael S. Rogers to take over as head of the NSA and Pentagon's Cyber Command, following the retirement of embattled current NSA director Gen. Keith. B. Alexander. Though Pentagon and White House officials emphasized Rogers' technical and administrative qualifications for the job, Rogers is on record as advocating a "warrior ethos" among military cyber-security crews that would encourage use of military networks and other digital resources as weapons rather than just infrastructure to be maintained. Moscow's Jan. 30 announcement that it would create a defensive cyber-force was not the first time Russian officials have complained about online attacks, or announced plans to beef up defense against them using both the secret police and the military. RIA Novosti reported in April that the Russian Interior Ministry would spend the equivalent of $1.3 million on security to prevent attacks on its computer networks and to link with similar intrusion-prevention systems used by the Russian Federal Security Service (FSB) – the post-Soviet ancestor of the KGB. Russian officials complained at the time that Websites belonging to the office of the President and two houses of the Russian parliament sustained up to 10,000 attacks every day. A more serious reason may be the virus, dubbed "Red October," that was discovered infecting Russian government systems with programming designed to "gather sensitive documents," according to an advisory from Kaspersky Labs, which published a report on the virus Jan. 14, 2013. The virus had been active since at least 2007, was most concentrated in diplomatic and government agencies of various countries, and was spread by malware identified as "Rocra," which carried a variable payload that could include information-stealing modules and Trojans to create backdoors into secure systems. Rocra and Red October are part of a "high-level cyber-espionage campaign has successfully infiltrated computer networks at diplomatic, governmental and scientific research organizations," according to the Kaspersky analysis. Red October's sophistication and effectiveness is nearly as great as that of the "Flame" malware – an attack toolkit even more sophisticated that the Duqu and Stuxnet viruses that were designed to attack nuclear-development facilities in Iran, according to Kaspersky. Flame, which is believed to have been created by a state-sponsored intelligence agency, "pretty much redefines the notion of cyberwar and cyberespionage," according to a May 2013 Kaspersky analysis. Russian President Vladimir Putin responded to news of the Red October virus by ordering the FSB to create a system designed to identify and prevent cyberattacks, and by proposing a cooperative anti-cybercrime enforcement agreement with China, according to RIA Novosti. Russian military officials announced in August they were creating a special cyber warfare unit that would become active as early as 2014 to prepare for the potential of the Internet to become "a theater of war." "The world is getting ready for a new arms race—this time in cyber weapons," according to a June 26 article by RIA Novosti commentator Konstantin Bogdanov. In the piece, Bogdanov accused U.S. intelligence agencies under Presidential Administration of George W. Bush of having created and launched not only Duqu, Stuxnet and Flame, but of weaponizing the Internet and launching a new arms race in cyberspace. "What was previously considered to be the domain of semi-criminal marginal groups or a cheap way of expressing sociopathy is now attracting the interest of governments, who are considering producing weaponized software on an industrial scale," Bogdanov wrote. The effort is rash, provocative and dangerous, Bogdanov warned, under the heading, "Don't play with matches at a gas station," in which he compared the current state of militarized malware to the period between July 16 1945 and Aug. 6, 1945, "after the United States tested its first nuclear device near Alamagordo [N.M.] but had not yet dropped any nuclear bombs on Japanese cities." Though Russian officials resolutely accuse U.S. agencies of being the main force behind state-sponsored cyberwar and cyber-espionage, Russian agencies have never been shy about online intrusions and have stepped up their activities during the past decade, according to U.S.-based security analysis firm CrowdStrike. In a report summarizing cyber-espionage activity by 50 "cyber threat actors," CrowdStrike noted a sharp increase in attacks from the Russian group nicknamed "Energetic Bear." During the past two years, Russian groups have used an increasingly sophisticated menu of tools and techniques to penetrate energy companies, defense contractors, technology companies and government agencies in Europe, Asia and the U.S., acquiring information of political or military interest, but also expanding into good old-fashioned industrial espionage. CrowdStrike characterized 34 of the 41 primary "cyberadversaries" it identified in the report as being nation-states. "Observed indicators obtained from monitoring this adversary's activity suggest that Energetic Bear is operating out of Russia, or at least on behalf of Russia-based interests, and it is possible that their operations are carried out with the sponsorship and knowledge of the Russian state," the CrowdStrike report concluded. Image: Kaspersky Labs Russian Cyberwar Force Intensifies 'net Arms Race
[caption id="attachment_16861" align="aligncenter" width="564"]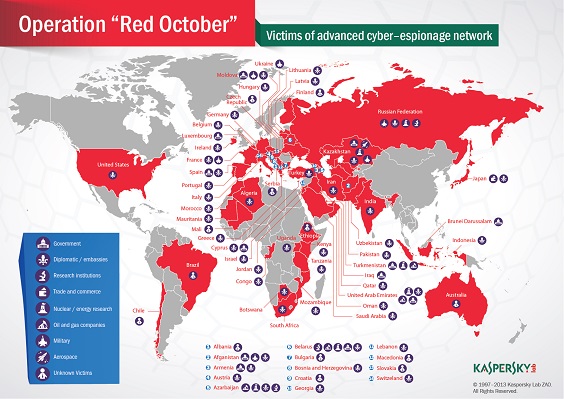 'Red October' attack may have touched off global online arms race.[/caption] On the same day the Obama Administration revealed its pick for the new head of the National Security Agency (NSA), Russian officials announced they will launch a new military unit devoted to keeping digital attacks from crippling the Russian military. The new cyberdefense unit, which is due to go into operation by 2017, will be created "to defend Russian armed forces' critical infrastructure from computer attacks," according to Maj. Gen. Yuri Kuznetsov, who was quoted in the state-backed RIA Novosti news agency. It may or may not be coincidence that Kuznetsov's announcement came on the same day the White House leaked its plan to appoint U.S. Navy Vice Admiral Michael S. Rogers to take over as head of the NSA and Pentagon's Cyber Command, following the retirement of embattled current NSA director Gen. Keith. B. Alexander. Though Pentagon and White House officials emphasized Rogers' technical and administrative qualifications for the job, Rogers is on record as advocating a "warrior ethos" among military cyber-security crews that would encourage use of military networks and other digital resources as weapons rather than just infrastructure to be maintained. Moscow's Jan. 30 announcement that it would create a defensive cyber-force was not the first time Russian officials have complained about online attacks, or announced plans to beef up defense against them using both the secret police and the military. RIA Novosti reported in April that the Russian Interior Ministry would spend the equivalent of $1.3 million on security to prevent attacks on its computer networks and to link with similar intrusion-prevention systems used by the Russian Federal Security Service (FSB) – the post-Soviet ancestor of the KGB. Russian officials complained at the time that Websites belonging to the office of the President and two houses of the Russian parliament sustained up to 10,000 attacks every day. A more serious reason may be the virus, dubbed "Red October," that was discovered infecting Russian government systems with programming designed to "gather sensitive documents," according to an advisory from Kaspersky Labs, which published a report on the virus Jan. 14, 2013. The virus had been active since at least 2007, was most concentrated in diplomatic and government agencies of various countries, and was spread by malware identified as "Rocra," which carried a variable payload that could include information-stealing modules and Trojans to create backdoors into secure systems. Rocra and Red October are part of a "high-level cyber-espionage campaign has successfully infiltrated computer networks at diplomatic, governmental and scientific research organizations," according to the Kaspersky analysis. Red October's sophistication and effectiveness is nearly as great as that of the "Flame" malware – an attack toolkit even more sophisticated that the Duqu and Stuxnet viruses that were designed to attack nuclear-development facilities in Iran, according to Kaspersky. Flame, which is believed to have been created by a state-sponsored intelligence agency, "pretty much redefines the notion of cyberwar and cyberespionage," according to a May 2013 Kaspersky analysis. Russian President Vladimir Putin responded to news of the Red October virus by ordering the FSB to create a system designed to identify and prevent cyberattacks, and by proposing a cooperative anti-cybercrime enforcement agreement with China, according to RIA Novosti. Russian military officials announced in August they were creating a special cyber warfare unit that would become active as early as 2014 to prepare for the potential of the Internet to become "a theater of war." "The world is getting ready for a new arms race—this time in cyber weapons," according to a June 26 article by RIA Novosti commentator Konstantin Bogdanov. In the piece, Bogdanov accused U.S. intelligence agencies under Presidential Administration of George W. Bush of having created and launched not only Duqu, Stuxnet and Flame, but of weaponizing the Internet and launching a new arms race in cyberspace. "What was previously considered to be the domain of semi-criminal marginal groups or a cheap way of expressing sociopathy is now attracting the interest of governments, who are considering producing weaponized software on an industrial scale," Bogdanov wrote. The effort is rash, provocative and dangerous, Bogdanov warned, under the heading, "Don't play with matches at a gas station," in which he compared the current state of militarized malware to the period between July 16 1945 and Aug. 6, 1945, "after the United States tested its first nuclear device near Alamagordo [N.M.] but had not yet dropped any nuclear bombs on Japanese cities." Though Russian officials resolutely accuse U.S. agencies of being the main force behind state-sponsored cyberwar and cyber-espionage, Russian agencies have never been shy about online intrusions and have stepped up their activities during the past decade, according to U.S.-based security analysis firm CrowdStrike. In a report summarizing cyber-espionage activity by 50 "cyber threat actors," CrowdStrike noted a sharp increase in attacks from the Russian group nicknamed "Energetic Bear." During the past two years, Russian groups have used an increasingly sophisticated menu of tools and techniques to penetrate energy companies, defense contractors, technology companies and government agencies in Europe, Asia and the U.S., acquiring information of political or military interest, but also expanding into good old-fashioned industrial espionage. CrowdStrike characterized 34 of the 41 primary "cyberadversaries" it identified in the report as being nation-states. "Observed indicators obtained from monitoring this adversary's activity suggest that Energetic Bear is operating out of Russia, or at least on behalf of Russia-based interests, and it is possible that their operations are carried out with the sponsorship and knowledge of the Russian state," the CrowdStrike report concluded. Image: Kaspersky Labs
'Red October' attack may have touched off global online arms race.[/caption] On the same day the Obama Administration revealed its pick for the new head of the National Security Agency (NSA), Russian officials announced they will launch a new military unit devoted to keeping digital attacks from crippling the Russian military. The new cyberdefense unit, which is due to go into operation by 2017, will be created "to defend Russian armed forces' critical infrastructure from computer attacks," according to Maj. Gen. Yuri Kuznetsov, who was quoted in the state-backed RIA Novosti news agency. It may or may not be coincidence that Kuznetsov's announcement came on the same day the White House leaked its plan to appoint U.S. Navy Vice Admiral Michael S. Rogers to take over as head of the NSA and Pentagon's Cyber Command, following the retirement of embattled current NSA director Gen. Keith. B. Alexander. Though Pentagon and White House officials emphasized Rogers' technical and administrative qualifications for the job, Rogers is on record as advocating a "warrior ethos" among military cyber-security crews that would encourage use of military networks and other digital resources as weapons rather than just infrastructure to be maintained. Moscow's Jan. 30 announcement that it would create a defensive cyber-force was not the first time Russian officials have complained about online attacks, or announced plans to beef up defense against them using both the secret police and the military. RIA Novosti reported in April that the Russian Interior Ministry would spend the equivalent of $1.3 million on security to prevent attacks on its computer networks and to link with similar intrusion-prevention systems used by the Russian Federal Security Service (FSB) – the post-Soviet ancestor of the KGB. Russian officials complained at the time that Websites belonging to the office of the President and two houses of the Russian parliament sustained up to 10,000 attacks every day. A more serious reason may be the virus, dubbed "Red October," that was discovered infecting Russian government systems with programming designed to "gather sensitive documents," according to an advisory from Kaspersky Labs, which published a report on the virus Jan. 14, 2013. The virus had been active since at least 2007, was most concentrated in diplomatic and government agencies of various countries, and was spread by malware identified as "Rocra," which carried a variable payload that could include information-stealing modules and Trojans to create backdoors into secure systems. Rocra and Red October are part of a "high-level cyber-espionage campaign has successfully infiltrated computer networks at diplomatic, governmental and scientific research organizations," according to the Kaspersky analysis. Red October's sophistication and effectiveness is nearly as great as that of the "Flame" malware – an attack toolkit even more sophisticated that the Duqu and Stuxnet viruses that were designed to attack nuclear-development facilities in Iran, according to Kaspersky. Flame, which is believed to have been created by a state-sponsored intelligence agency, "pretty much redefines the notion of cyberwar and cyberespionage," according to a May 2013 Kaspersky analysis. Russian President Vladimir Putin responded to news of the Red October virus by ordering the FSB to create a system designed to identify and prevent cyberattacks, and by proposing a cooperative anti-cybercrime enforcement agreement with China, according to RIA Novosti. Russian military officials announced in August they were creating a special cyber warfare unit that would become active as early as 2014 to prepare for the potential of the Internet to become "a theater of war." "The world is getting ready for a new arms race—this time in cyber weapons," according to a June 26 article by RIA Novosti commentator Konstantin Bogdanov. In the piece, Bogdanov accused U.S. intelligence agencies under Presidential Administration of George W. Bush of having created and launched not only Duqu, Stuxnet and Flame, but of weaponizing the Internet and launching a new arms race in cyberspace. "What was previously considered to be the domain of semi-criminal marginal groups or a cheap way of expressing sociopathy is now attracting the interest of governments, who are considering producing weaponized software on an industrial scale," Bogdanov wrote. The effort is rash, provocative and dangerous, Bogdanov warned, under the heading, "Don't play with matches at a gas station," in which he compared the current state of militarized malware to the period between July 16 1945 and Aug. 6, 1945, "after the United States tested its first nuclear device near Alamagordo [N.M.] but had not yet dropped any nuclear bombs on Japanese cities." Though Russian officials resolutely accuse U.S. agencies of being the main force behind state-sponsored cyberwar and cyber-espionage, Russian agencies have never been shy about online intrusions and have stepped up their activities during the past decade, according to U.S.-based security analysis firm CrowdStrike. In a report summarizing cyber-espionage activity by 50 "cyber threat actors," CrowdStrike noted a sharp increase in attacks from the Russian group nicknamed "Energetic Bear." During the past two years, Russian groups have used an increasingly sophisticated menu of tools and techniques to penetrate energy companies, defense contractors, technology companies and government agencies in Europe, Asia and the U.S., acquiring information of political or military interest, but also expanding into good old-fashioned industrial espionage. CrowdStrike characterized 34 of the 41 primary "cyberadversaries" it identified in the report as being nation-states. "Observed indicators obtained from monitoring this adversary's activity suggest that Energetic Bear is operating out of Russia, or at least on behalf of Russia-based interests, and it is possible that their operations are carried out with the sponsorship and knowledge of the Russian state," the CrowdStrike report concluded. Image: Kaspersky Labs
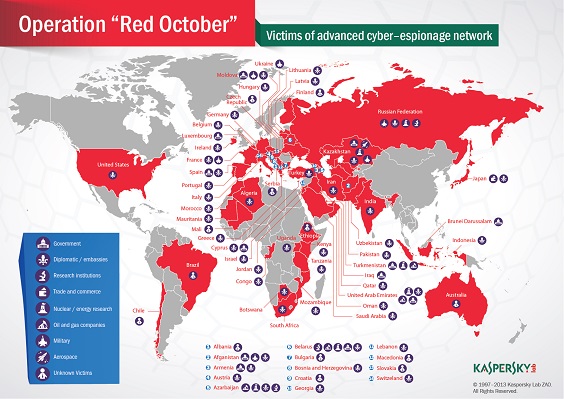 'Red October' attack may have touched off global online arms race.[/caption] On the same day the Obama Administration revealed its pick for the new head of the National Security Agency (NSA), Russian officials announced they will launch a new military unit devoted to keeping digital attacks from crippling the Russian military. The new cyberdefense unit, which is due to go into operation by 2017, will be created "to defend Russian armed forces' critical infrastructure from computer attacks," according to Maj. Gen. Yuri Kuznetsov, who was quoted in the state-backed RIA Novosti news agency. It may or may not be coincidence that Kuznetsov's announcement came on the same day the White House leaked its plan to appoint U.S. Navy Vice Admiral Michael S. Rogers to take over as head of the NSA and Pentagon's Cyber Command, following the retirement of embattled current NSA director Gen. Keith. B. Alexander. Though Pentagon and White House officials emphasized Rogers' technical and administrative qualifications for the job, Rogers is on record as advocating a "warrior ethos" among military cyber-security crews that would encourage use of military networks and other digital resources as weapons rather than just infrastructure to be maintained. Moscow's Jan. 30 announcement that it would create a defensive cyber-force was not the first time Russian officials have complained about online attacks, or announced plans to beef up defense against them using both the secret police and the military. RIA Novosti reported in April that the Russian Interior Ministry would spend the equivalent of $1.3 million on security to prevent attacks on its computer networks and to link with similar intrusion-prevention systems used by the Russian Federal Security Service (FSB) – the post-Soviet ancestor of the KGB. Russian officials complained at the time that Websites belonging to the office of the President and two houses of the Russian parliament sustained up to 10,000 attacks every day. A more serious reason may be the virus, dubbed "Red October," that was discovered infecting Russian government systems with programming designed to "gather sensitive documents," according to an advisory from Kaspersky Labs, which published a report on the virus Jan. 14, 2013. The virus had been active since at least 2007, was most concentrated in diplomatic and government agencies of various countries, and was spread by malware identified as "Rocra," which carried a variable payload that could include information-stealing modules and Trojans to create backdoors into secure systems. Rocra and Red October are part of a "high-level cyber-espionage campaign has successfully infiltrated computer networks at diplomatic, governmental and scientific research organizations," according to the Kaspersky analysis. Red October's sophistication and effectiveness is nearly as great as that of the "Flame" malware – an attack toolkit even more sophisticated that the Duqu and Stuxnet viruses that were designed to attack nuclear-development facilities in Iran, according to Kaspersky. Flame, which is believed to have been created by a state-sponsored intelligence agency, "pretty much redefines the notion of cyberwar and cyberespionage," according to a May 2013 Kaspersky analysis. Russian President Vladimir Putin responded to news of the Red October virus by ordering the FSB to create a system designed to identify and prevent cyberattacks, and by proposing a cooperative anti-cybercrime enforcement agreement with China, according to RIA Novosti. Russian military officials announced in August they were creating a special cyber warfare unit that would become active as early as 2014 to prepare for the potential of the Internet to become "a theater of war." "The world is getting ready for a new arms race—this time in cyber weapons," according to a June 26 article by RIA Novosti commentator Konstantin Bogdanov. In the piece, Bogdanov accused U.S. intelligence agencies under Presidential Administration of George W. Bush of having created and launched not only Duqu, Stuxnet and Flame, but of weaponizing the Internet and launching a new arms race in cyberspace. "What was previously considered to be the domain of semi-criminal marginal groups or a cheap way of expressing sociopathy is now attracting the interest of governments, who are considering producing weaponized software on an industrial scale," Bogdanov wrote. The effort is rash, provocative and dangerous, Bogdanov warned, under the heading, "Don't play with matches at a gas station," in which he compared the current state of militarized malware to the period between July 16 1945 and Aug. 6, 1945, "after the United States tested its first nuclear device near Alamagordo [N.M.] but had not yet dropped any nuclear bombs on Japanese cities." Though Russian officials resolutely accuse U.S. agencies of being the main force behind state-sponsored cyberwar and cyber-espionage, Russian agencies have never been shy about online intrusions and have stepped up their activities during the past decade, according to U.S.-based security analysis firm CrowdStrike. In a report summarizing cyber-espionage activity by 50 "cyber threat actors," CrowdStrike noted a sharp increase in attacks from the Russian group nicknamed "Energetic Bear." During the past two years, Russian groups have used an increasingly sophisticated menu of tools and techniques to penetrate energy companies, defense contractors, technology companies and government agencies in Europe, Asia and the U.S., acquiring information of political or military interest, but also expanding into good old-fashioned industrial espionage. CrowdStrike characterized 34 of the 41 primary "cyberadversaries" it identified in the report as being nation-states. "Observed indicators obtained from monitoring this adversary's activity suggest that Energetic Bear is operating out of Russia, or at least on behalf of Russia-based interests, and it is possible that their operations are carried out with the sponsorship and knowledge of the Russian state," the CrowdStrike report concluded. Image: Kaspersky Labs
'Red October' attack may have touched off global online arms race.[/caption] On the same day the Obama Administration revealed its pick for the new head of the National Security Agency (NSA), Russian officials announced they will launch a new military unit devoted to keeping digital attacks from crippling the Russian military. The new cyberdefense unit, which is due to go into operation by 2017, will be created "to defend Russian armed forces' critical infrastructure from computer attacks," according to Maj. Gen. Yuri Kuznetsov, who was quoted in the state-backed RIA Novosti news agency. It may or may not be coincidence that Kuznetsov's announcement came on the same day the White House leaked its plan to appoint U.S. Navy Vice Admiral Michael S. Rogers to take over as head of the NSA and Pentagon's Cyber Command, following the retirement of embattled current NSA director Gen. Keith. B. Alexander. Though Pentagon and White House officials emphasized Rogers' technical and administrative qualifications for the job, Rogers is on record as advocating a "warrior ethos" among military cyber-security crews that would encourage use of military networks and other digital resources as weapons rather than just infrastructure to be maintained. Moscow's Jan. 30 announcement that it would create a defensive cyber-force was not the first time Russian officials have complained about online attacks, or announced plans to beef up defense against them using both the secret police and the military. RIA Novosti reported in April that the Russian Interior Ministry would spend the equivalent of $1.3 million on security to prevent attacks on its computer networks and to link with similar intrusion-prevention systems used by the Russian Federal Security Service (FSB) – the post-Soviet ancestor of the KGB. Russian officials complained at the time that Websites belonging to the office of the President and two houses of the Russian parliament sustained up to 10,000 attacks every day. A more serious reason may be the virus, dubbed "Red October," that was discovered infecting Russian government systems with programming designed to "gather sensitive documents," according to an advisory from Kaspersky Labs, which published a report on the virus Jan. 14, 2013. The virus had been active since at least 2007, was most concentrated in diplomatic and government agencies of various countries, and was spread by malware identified as "Rocra," which carried a variable payload that could include information-stealing modules and Trojans to create backdoors into secure systems. Rocra and Red October are part of a "high-level cyber-espionage campaign has successfully infiltrated computer networks at diplomatic, governmental and scientific research organizations," according to the Kaspersky analysis. Red October's sophistication and effectiveness is nearly as great as that of the "Flame" malware – an attack toolkit even more sophisticated that the Duqu and Stuxnet viruses that were designed to attack nuclear-development facilities in Iran, according to Kaspersky. Flame, which is believed to have been created by a state-sponsored intelligence agency, "pretty much redefines the notion of cyberwar and cyberespionage," according to a May 2013 Kaspersky analysis. Russian President Vladimir Putin responded to news of the Red October virus by ordering the FSB to create a system designed to identify and prevent cyberattacks, and by proposing a cooperative anti-cybercrime enforcement agreement with China, according to RIA Novosti. Russian military officials announced in August they were creating a special cyber warfare unit that would become active as early as 2014 to prepare for the potential of the Internet to become "a theater of war." "The world is getting ready for a new arms race—this time in cyber weapons," according to a June 26 article by RIA Novosti commentator Konstantin Bogdanov. In the piece, Bogdanov accused U.S. intelligence agencies under Presidential Administration of George W. Bush of having created and launched not only Duqu, Stuxnet and Flame, but of weaponizing the Internet and launching a new arms race in cyberspace. "What was previously considered to be the domain of semi-criminal marginal groups or a cheap way of expressing sociopathy is now attracting the interest of governments, who are considering producing weaponized software on an industrial scale," Bogdanov wrote. The effort is rash, provocative and dangerous, Bogdanov warned, under the heading, "Don't play with matches at a gas station," in which he compared the current state of militarized malware to the period between July 16 1945 and Aug. 6, 1945, "after the United States tested its first nuclear device near Alamagordo [N.M.] but had not yet dropped any nuclear bombs on Japanese cities." Though Russian officials resolutely accuse U.S. agencies of being the main force behind state-sponsored cyberwar and cyber-espionage, Russian agencies have never been shy about online intrusions and have stepped up their activities during the past decade, according to U.S.-based security analysis firm CrowdStrike. In a report summarizing cyber-espionage activity by 50 "cyber threat actors," CrowdStrike noted a sharp increase in attacks from the Russian group nicknamed "Energetic Bear." During the past two years, Russian groups have used an increasingly sophisticated menu of tools and techniques to penetrate energy companies, defense contractors, technology companies and government agencies in Europe, Asia and the U.S., acquiring information of political or military interest, but also expanding into good old-fashioned industrial espionage. CrowdStrike characterized 34 of the 41 primary "cyberadversaries" it identified in the report as being nation-states. "Observed indicators obtained from monitoring this adversary's activity suggest that Energetic Bear is operating out of Russia, or at least on behalf of Russia-based interests, and it is possible that their operations are carried out with the sponsorship and knowledge of the Russian state," the CrowdStrike report concluded. Image: Kaspersky Labs