[caption id="attachment_16564" align="aligncenter" width="600"]
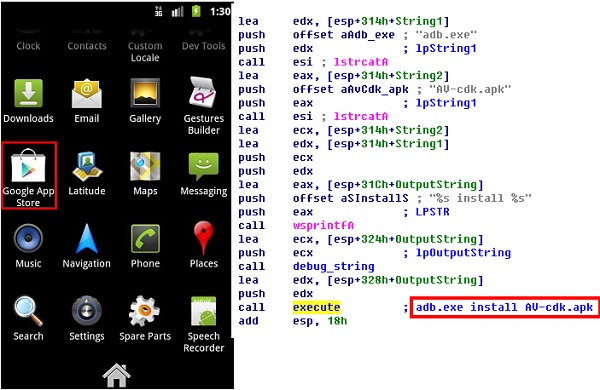
Trojan acts as a wrapper in order to load Android malware.[/caption] A bit of malware discovered by researchers at Symantec this week reverses the target-selection priorities of most malware designs by treating Windows-based PCs as a path to Android devices, rather than as the primary target. "We’ve seen Android malware that attempts to infect Windows systems before," according to a
blog entry posted Jan. 23 by Symantec researcher Flora Liu. "We recently came across something that works the other way round: a Windows threat that attempts to infect Android devices." The multi-stage malware, called Trojan.Droidpak, is designed to infect a Windows machine using a malicious DLL, which downloads a APK of villainous intent that it tries to install on any Android device that connects to the Windows machine, Liu wrote. Trojan.Droidpak appears to be a wrapper for a better-known mobile-banking software-scamming malware called Android.Fakebank.B, which targets mobile-banking apps. The current version targets only apps from certain Korean banks,
according to an Oct. 13 Symantec malware update, but could be modified to attack other apps as well. Trojan.Droidpak – for which the technical details and removal procedures are
listed here – uses Windows' autorun to launch itself. It registers itself as a system service, then downloads a configuration file called iconfig.txt, which it uses to download the Android malware. It stores the malicious APK in the Windows directory of the compromised PC as AV-cdk.apk, within the newly created subdirectory %Windir%CrainingApkConfig. The Windows-executable either downloads the
Android Debug Bridge (ADB) or uses a resident version of the app-installation and management tool to install the AV-CDK. Apk malware file on any Android device that connects to the Windows machine. Once installed, the malware disguises itself with the name and icon of the Google App Store application, then searches for specific Korean mobile-banking applications and tries to replace the legitimate apps with malicious versions of its own. The APK appears to be similar or identical to Android.Fakebank.B, which uses SMS to send the device phone number to a command-and-control server (CnC), then copies later SMS messages to a list of other CnC addresses, Liu added. Fakebank.B targets the following banking applications:
- nh.smart
- com.shinhan.sbanking
- com.webcash.wooribank
- com.ATsolution.KBbank
- com.hanabank.ebk.channel.android.hananbank
Trojan.Droidpak creates the file %System%flashmx32.xtl on windows machines and registers itself using the following registry entry: HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServicesflashmx. Symantec's recommendations to avoid infection are the usual best-practice security rules, including disabling Windows Autorun for CDs and USBs. The Trojan is not widespread or difficult to remove using standard anti-virus scans, according to Liu's assessment
and that of other anti-virus providers. But the payload itself opens a backdoor in an Android device, so it could pose a risk even to devices not running Korean mobile-banking software. The real danger is that Trojan.Droidpak acts as a wrapper that could be adapted to carry other malicious payloads, and offer a method of infecting an Android device few users and even most security applications don't look for specifically. That could mean trouble in the future even for users who practice good app-installation hygiene on their Android devices, but don't expect to be infected simply by connecting to their own laptops.
Image: Symantec 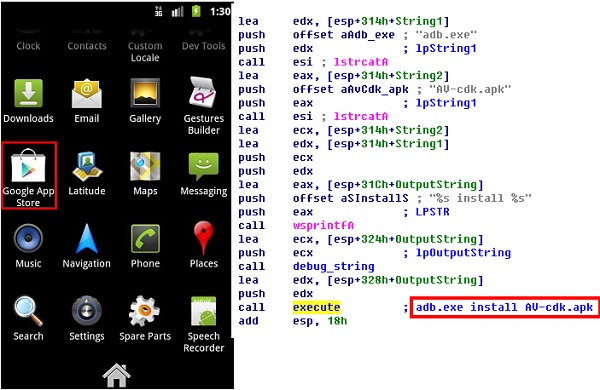 Trojan acts as a wrapper in order to load Android malware.[/caption] A bit of malware discovered by researchers at Symantec this week reverses the target-selection priorities of most malware designs by treating Windows-based PCs as a path to Android devices, rather than as the primary target. "We’ve seen Android malware that attempts to infect Windows systems before," according to a blog entry posted Jan. 23 by Symantec researcher Flora Liu. "We recently came across something that works the other way round: a Windows threat that attempts to infect Android devices." The multi-stage malware, called Trojan.Droidpak, is designed to infect a Windows machine using a malicious DLL, which downloads a APK of villainous intent that it tries to install on any Android device that connects to the Windows machine, Liu wrote. Trojan.Droidpak appears to be a wrapper for a better-known mobile-banking software-scamming malware called Android.Fakebank.B, which targets mobile-banking apps. The current version targets only apps from certain Korean banks, according to an Oct. 13 Symantec malware update, but could be modified to attack other apps as well. Trojan.Droidpak – for which the technical details and removal procedures are listed here – uses Windows' autorun to launch itself. It registers itself as a system service, then downloads a configuration file called iconfig.txt, which it uses to download the Android malware. It stores the malicious APK in the Windows directory of the compromised PC as AV-cdk.apk, within the newly created subdirectory %Windir%CrainingApkConfig. The Windows-executable either downloads the Android Debug Bridge (ADB) or uses a resident version of the app-installation and management tool to install the AV-CDK. Apk malware file on any Android device that connects to the Windows machine. Once installed, the malware disguises itself with the name and icon of the Google App Store application, then searches for specific Korean mobile-banking applications and tries to replace the legitimate apps with malicious versions of its own. The APK appears to be similar or identical to Android.Fakebank.B, which uses SMS to send the device phone number to a command-and-control server (CnC), then copies later SMS messages to a list of other CnC addresses, Liu added. Fakebank.B targets the following banking applications:
Trojan acts as a wrapper in order to load Android malware.[/caption] A bit of malware discovered by researchers at Symantec this week reverses the target-selection priorities of most malware designs by treating Windows-based PCs as a path to Android devices, rather than as the primary target. "We’ve seen Android malware that attempts to infect Windows systems before," according to a blog entry posted Jan. 23 by Symantec researcher Flora Liu. "We recently came across something that works the other way round: a Windows threat that attempts to infect Android devices." The multi-stage malware, called Trojan.Droidpak, is designed to infect a Windows machine using a malicious DLL, which downloads a APK of villainous intent that it tries to install on any Android device that connects to the Windows machine, Liu wrote. Trojan.Droidpak appears to be a wrapper for a better-known mobile-banking software-scamming malware called Android.Fakebank.B, which targets mobile-banking apps. The current version targets only apps from certain Korean banks, according to an Oct. 13 Symantec malware update, but could be modified to attack other apps as well. Trojan.Droidpak – for which the technical details and removal procedures are listed here – uses Windows' autorun to launch itself. It registers itself as a system service, then downloads a configuration file called iconfig.txt, which it uses to download the Android malware. It stores the malicious APK in the Windows directory of the compromised PC as AV-cdk.apk, within the newly created subdirectory %Windir%CrainingApkConfig. The Windows-executable either downloads the Android Debug Bridge (ADB) or uses a resident version of the app-installation and management tool to install the AV-CDK. Apk malware file on any Android device that connects to the Windows machine. Once installed, the malware disguises itself with the name and icon of the Google App Store application, then searches for specific Korean mobile-banking applications and tries to replace the legitimate apps with malicious versions of its own. The APK appears to be similar or identical to Android.Fakebank.B, which uses SMS to send the device phone number to a command-and-control server (CnC), then copies later SMS messages to a list of other CnC addresses, Liu added. Fakebank.B targets the following banking applications:


