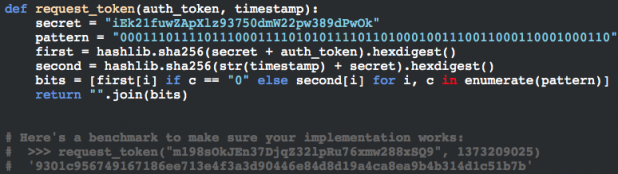
 Part of the code that could represent trouble for Snapchat.[/caption] Snapchat might not be so private after all. Cyber-security collective Gibson Security has revealed a pair of exploits in the messaging service’s code: one that allows hackers to figure out users’ private details, and another that could result in the mass generation of fake accounts for spamming purposes. If those loopholes are left unclosed, they could present a boon to stalkers and spammers—and an enormous embarrassment to Snapchat, whose business model is entirely dependent on users being able to send private messages that vaporize without a trace within a few seconds of opening. (Hat tip to ZDNet for the original link.) What’s worse, Gibson Security suggested it’s only going public with the exploits after Snapchat ignored its warnings. “Given that it's been around four months since our last Snapchat release, we figured we'd do a refresher on the latest version, and see which of the released exploits had been fixed (full disclosure: none of them),” the group wrote in a lengthy breakdown of its findings. “Seeing that nothing had been really been improved upon (although, stories are using AES/CBC rather than AES/ECB, which is a start), we decided that it was in everyone's best interests for us to post a full disclosure of everything we've found in our past months of hacking the gibson.” Since the summer, the collective claimed, “numerous public Snapchat API clients” have popped up on Github. “Thankfully, Snapchat are too busy declining ridiculously high offers from Facebook and Google,” they wrote, “and lying to investors (hint: they have no way to tell the genders of their users, see /bq/register for a lack of gender specification) to send unlawful code takedown requests to all the developers involved.” Gibson Security’s breakdown is based on Snapchat build 4.1.01 for Android, which relies on a combination of /ph and /bq endpoints. It includes some proof-of-concept scripts, which are likely causing any security personnel over at Snapchat’s headquarters no end of joy and merriment this holiday season. If the loopholes are verified, how long will the messaging service take to close them? Image: Gibson Security
Part of the code that could represent trouble for Snapchat.[/caption] Snapchat might not be so private after all. Cyber-security collective Gibson Security has revealed a pair of exploits in the messaging service’s code: one that allows hackers to figure out users’ private details, and another that could result in the mass generation of fake accounts for spamming purposes. If those loopholes are left unclosed, they could present a boon to stalkers and spammers—and an enormous embarrassment to Snapchat, whose business model is entirely dependent on users being able to send private messages that vaporize without a trace within a few seconds of opening. (Hat tip to ZDNet for the original link.) What’s worse, Gibson Security suggested it’s only going public with the exploits after Snapchat ignored its warnings. “Given that it's been around four months since our last Snapchat release, we figured we'd do a refresher on the latest version, and see which of the released exploits had been fixed (full disclosure: none of them),” the group wrote in a lengthy breakdown of its findings. “Seeing that nothing had been really been improved upon (although, stories are using AES/CBC rather than AES/ECB, which is a start), we decided that it was in everyone's best interests for us to post a full disclosure of everything we've found in our past months of hacking the gibson.” Since the summer, the collective claimed, “numerous public Snapchat API clients” have popped up on Github. “Thankfully, Snapchat are too busy declining ridiculously high offers from Facebook and Google,” they wrote, “and lying to investors (hint: they have no way to tell the genders of their users, see /bq/register for a lack of gender specification) to send unlawful code takedown requests to all the developers involved.” Gibson Security’s breakdown is based on Snapchat build 4.1.01 for Android, which relies on a combination of /ph and /bq endpoints. It includes some proof-of-concept scripts, which are likely causing any security personnel over at Snapchat’s headquarters no end of joy and merriment this holiday season. If the loopholes are verified, how long will the messaging service take to close them? Image: Gibson Security Snapchat Exploits Could Reveal Private User Details
[caption id="attachment_15542" align="aligncenter" width="618"] 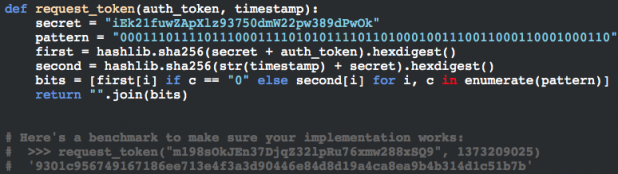 Part of the code that could represent trouble for Snapchat.[/caption] Snapchat might not be so private after all. Cyber-security collective Gibson Security has revealed a pair of exploits in the messaging service’s code: one that allows hackers to figure out users’ private details, and another that could result in the mass generation of fake accounts for spamming purposes. If those loopholes are left unclosed, they could present a boon to stalkers and spammers—and an enormous embarrassment to Snapchat, whose business model is entirely dependent on users being able to send private messages that vaporize without a trace within a few seconds of opening. (Hat tip to ZDNet for the original link.) What’s worse, Gibson Security suggested it’s only going public with the exploits after Snapchat ignored its warnings. “Given that it's been around four months since our last Snapchat release, we figured we'd do a refresher on the latest version, and see which of the released exploits had been fixed (full disclosure: none of them),” the group wrote in a lengthy breakdown of its findings. “Seeing that nothing had been really been improved upon (although, stories are using AES/CBC rather than AES/ECB, which is a start), we decided that it was in everyone's best interests for us to post a full disclosure of everything we've found in our past months of hacking the gibson.” Since the summer, the collective claimed, “numerous public Snapchat API clients” have popped up on Github. “Thankfully, Snapchat are too busy declining ridiculously high offers from Facebook and Google,” they wrote, “and lying to investors (hint: they have no way to tell the genders of their users, see /bq/register for a lack of gender specification) to send unlawful code takedown requests to all the developers involved.” Gibson Security’s breakdown is based on Snapchat build 4.1.01 for Android, which relies on a combination of /ph and /bq endpoints. It includes some proof-of-concept scripts, which are likely causing any security personnel over at Snapchat’s headquarters no end of joy and merriment this holiday season. If the loopholes are verified, how long will the messaging service take to close them? Image: Gibson Security
Part of the code that could represent trouble for Snapchat.[/caption] Snapchat might not be so private after all. Cyber-security collective Gibson Security has revealed a pair of exploits in the messaging service’s code: one that allows hackers to figure out users’ private details, and another that could result in the mass generation of fake accounts for spamming purposes. If those loopholes are left unclosed, they could present a boon to stalkers and spammers—and an enormous embarrassment to Snapchat, whose business model is entirely dependent on users being able to send private messages that vaporize without a trace within a few seconds of opening. (Hat tip to ZDNet for the original link.) What’s worse, Gibson Security suggested it’s only going public with the exploits after Snapchat ignored its warnings. “Given that it's been around four months since our last Snapchat release, we figured we'd do a refresher on the latest version, and see which of the released exploits had been fixed (full disclosure: none of them),” the group wrote in a lengthy breakdown of its findings. “Seeing that nothing had been really been improved upon (although, stories are using AES/CBC rather than AES/ECB, which is a start), we decided that it was in everyone's best interests for us to post a full disclosure of everything we've found in our past months of hacking the gibson.” Since the summer, the collective claimed, “numerous public Snapchat API clients” have popped up on Github. “Thankfully, Snapchat are too busy declining ridiculously high offers from Facebook and Google,” they wrote, “and lying to investors (hint: they have no way to tell the genders of their users, see /bq/register for a lack of gender specification) to send unlawful code takedown requests to all the developers involved.” Gibson Security’s breakdown is based on Snapchat build 4.1.01 for Android, which relies on a combination of /ph and /bq endpoints. It includes some proof-of-concept scripts, which are likely causing any security personnel over at Snapchat’s headquarters no end of joy and merriment this holiday season. If the loopholes are verified, how long will the messaging service take to close them? Image: Gibson Security
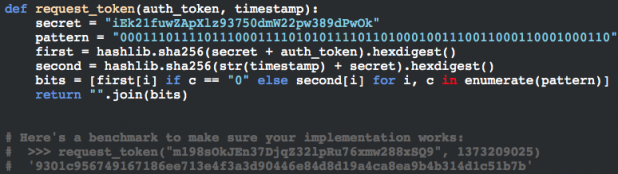 Part of the code that could represent trouble for Snapchat.[/caption] Snapchat might not be so private after all. Cyber-security collective Gibson Security has revealed a pair of exploits in the messaging service’s code: one that allows hackers to figure out users’ private details, and another that could result in the mass generation of fake accounts for spamming purposes. If those loopholes are left unclosed, they could present a boon to stalkers and spammers—and an enormous embarrassment to Snapchat, whose business model is entirely dependent on users being able to send private messages that vaporize without a trace within a few seconds of opening. (Hat tip to ZDNet for the original link.) What’s worse, Gibson Security suggested it’s only going public with the exploits after Snapchat ignored its warnings. “Given that it's been around four months since our last Snapchat release, we figured we'd do a refresher on the latest version, and see which of the released exploits had been fixed (full disclosure: none of them),” the group wrote in a lengthy breakdown of its findings. “Seeing that nothing had been really been improved upon (although, stories are using AES/CBC rather than AES/ECB, which is a start), we decided that it was in everyone's best interests for us to post a full disclosure of everything we've found in our past months of hacking the gibson.” Since the summer, the collective claimed, “numerous public Snapchat API clients” have popped up on Github. “Thankfully, Snapchat are too busy declining ridiculously high offers from Facebook and Google,” they wrote, “and lying to investors (hint: they have no way to tell the genders of their users, see /bq/register for a lack of gender specification) to send unlawful code takedown requests to all the developers involved.” Gibson Security’s breakdown is based on Snapchat build 4.1.01 for Android, which relies on a combination of /ph and /bq endpoints. It includes some proof-of-concept scripts, which are likely causing any security personnel over at Snapchat’s headquarters no end of joy and merriment this holiday season. If the loopholes are verified, how long will the messaging service take to close them? Image: Gibson Security
Part of the code that could represent trouble for Snapchat.[/caption] Snapchat might not be so private after all. Cyber-security collective Gibson Security has revealed a pair of exploits in the messaging service’s code: one that allows hackers to figure out users’ private details, and another that could result in the mass generation of fake accounts for spamming purposes. If those loopholes are left unclosed, they could present a boon to stalkers and spammers—and an enormous embarrassment to Snapchat, whose business model is entirely dependent on users being able to send private messages that vaporize without a trace within a few seconds of opening. (Hat tip to ZDNet for the original link.) What’s worse, Gibson Security suggested it’s only going public with the exploits after Snapchat ignored its warnings. “Given that it's been around four months since our last Snapchat release, we figured we'd do a refresher on the latest version, and see which of the released exploits had been fixed (full disclosure: none of them),” the group wrote in a lengthy breakdown of its findings. “Seeing that nothing had been really been improved upon (although, stories are using AES/CBC rather than AES/ECB, which is a start), we decided that it was in everyone's best interests for us to post a full disclosure of everything we've found in our past months of hacking the gibson.” Since the summer, the collective claimed, “numerous public Snapchat API clients” have popped up on Github. “Thankfully, Snapchat are too busy declining ridiculously high offers from Facebook and Google,” they wrote, “and lying to investors (hint: they have no way to tell the genders of their users, see /bq/register for a lack of gender specification) to send unlawful code takedown requests to all the developers involved.” Gibson Security’s breakdown is based on Snapchat build 4.1.01 for Android, which relies on a combination of /ph and /bq endpoints. It includes some proof-of-concept scripts, which are likely causing any security personnel over at Snapchat’s headquarters no end of joy and merriment this holiday season. If the loopholes are verified, how long will the messaging service take to close them? Image: Gibson Security 