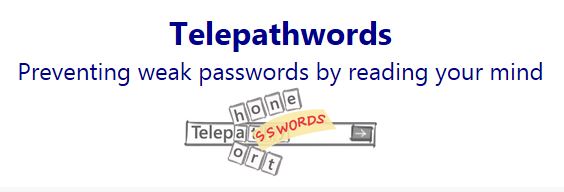
 New tool knows what makes passwords crackable and helps avoid them[/caption] Microsoft has posted a free online tool designed to check the security of passwords, or recommend more secure passwords that are also easier to type. Traditional rules requiring that "secure" passwords be case sensitive, include upper- and lower-case letters, digits and at least one non-alphanumeric character aren't nearly as effective at helping users create passwords that are hard to crack, according to Microsoft Research scientist Stuart Schechter. Most people follow those rules by using a name or word they can remember and swapping out characters until the security requirements are met. Turning "password1" into "P@$$w0rd1" isn't a big improvement, however, according to Schechter. Hackers know the rules at least as well as users and routinely try common passwords using both the proper and leet-speak spelling that supposedly makes them "secure," he said. Predictability, and not the upper-caseness or symbol-ization of certain letters, is what makes passwords weak, so the best passwords are those the user can remember but hackers can't guess. Critiquing existing passwords and creating new, unguessable ones are the design goals behind Telepathwords, a site based largely on Schechter's work gathering and analyzing huge lists of passwords, "secret" questions and other authentication data that became public after major data breaches (including those at Facebook, Google, Yahoo, Twitter, LinkedIn and others included in a list of more than 2 million passwords stolen from 93,000 sites). The passwords were stolen using a keylogger contained in a virus that began collecting logins Oct. 21, and was stopped Nov. 24 after researchers at security firm TrustWave found millions of passwords on a server in the Netherlands. A comparison with lists of passwords stolen in 2006 showed that the 10 most common passwords made up almost three times as large a percentage in 2013 as in 2006. Comparing the result with previous breaches, Schechter found that during the seven years since a major breach at MySpace in 2006, passwords have gotten even more predictable. In 2006 the 10 most common passwords made up .9 percent of the total number of passwords discovered. By 2013 it had gone up to 2.4 percent. Telepathwords knows that, as well as what the most common passwords are, how often they turn up, all the alternative spellings, what the less-common passwords are and their spellings and everything else Schechter could find out about the way end users create, spell and re-use passwords. "We saw firsthand the tricks people use to construct passwords and then figured out which ones we should assume attackers also know,” Schechter said. Just avoiding the most common passwords or tricks to mis-spell them would make the average password more secure, but Telepathwords' goal is to make them unguessable, which it tries to do one letter at a time. "The system doesn’t ask the user to learn anything up-front or follow any specific rules," Schechter wrote in a blog announcing the site. "Rather, as you type each key of your intended password, it displays the characters it thinks you’re most likely to type next. If it succeeds in predicting one or more characters of the rest of your password, the evidence that these characters are predictable will be right in front of your eyes." The site doesn't actually provide new passwords. It just shows how predictable each letter of a current password is and suggests alternatives. The Telepathwords project site is available here. It went live Dec. 5. Image:Microsoft Corp.
New tool knows what makes passwords crackable and helps avoid them[/caption] Microsoft has posted a free online tool designed to check the security of passwords, or recommend more secure passwords that are also easier to type. Traditional rules requiring that "secure" passwords be case sensitive, include upper- and lower-case letters, digits and at least one non-alphanumeric character aren't nearly as effective at helping users create passwords that are hard to crack, according to Microsoft Research scientist Stuart Schechter. Most people follow those rules by using a name or word they can remember and swapping out characters until the security requirements are met. Turning "password1" into "P@$$w0rd1" isn't a big improvement, however, according to Schechter. Hackers know the rules at least as well as users and routinely try common passwords using both the proper and leet-speak spelling that supposedly makes them "secure," he said. Predictability, and not the upper-caseness or symbol-ization of certain letters, is what makes passwords weak, so the best passwords are those the user can remember but hackers can't guess. Critiquing existing passwords and creating new, unguessable ones are the design goals behind Telepathwords, a site based largely on Schechter's work gathering and analyzing huge lists of passwords, "secret" questions and other authentication data that became public after major data breaches (including those at Facebook, Google, Yahoo, Twitter, LinkedIn and others included in a list of more than 2 million passwords stolen from 93,000 sites). The passwords were stolen using a keylogger contained in a virus that began collecting logins Oct. 21, and was stopped Nov. 24 after researchers at security firm TrustWave found millions of passwords on a server in the Netherlands. A comparison with lists of passwords stolen in 2006 showed that the 10 most common passwords made up almost three times as large a percentage in 2013 as in 2006. Comparing the result with previous breaches, Schechter found that during the seven years since a major breach at MySpace in 2006, passwords have gotten even more predictable. In 2006 the 10 most common passwords made up .9 percent of the total number of passwords discovered. By 2013 it had gone up to 2.4 percent. Telepathwords knows that, as well as what the most common passwords are, how often they turn up, all the alternative spellings, what the less-common passwords are and their spellings and everything else Schechter could find out about the way end users create, spell and re-use passwords. "We saw firsthand the tricks people use to construct passwords and then figured out which ones we should assume attackers also know,” Schechter said. Just avoiding the most common passwords or tricks to mis-spell them would make the average password more secure, but Telepathwords' goal is to make them unguessable, which it tries to do one letter at a time. "The system doesn’t ask the user to learn anything up-front or follow any specific rules," Schechter wrote in a blog announcing the site. "Rather, as you type each key of your intended password, it displays the characters it thinks you’re most likely to type next. If it succeeds in predicting one or more characters of the rest of your password, the evidence that these characters are predictable will be right in front of your eyes." The site doesn't actually provide new passwords. It just shows how predictable each letter of a current password is and suggests alternatives. The Telepathwords project site is available here. It went live Dec. 5. Image:Microsoft Corp. Telepathwords Makes Passwords Hard to Guess
[caption id="attachment_14923" align="aligncenter" width="564"]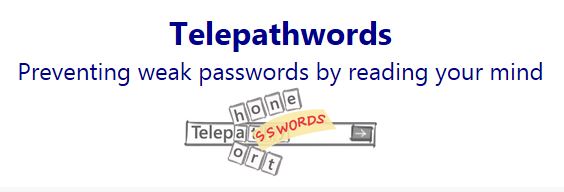 New tool knows what makes passwords crackable and helps avoid them[/caption] Microsoft has posted a free online tool designed to check the security of passwords, or recommend more secure passwords that are also easier to type. Traditional rules requiring that "secure" passwords be case sensitive, include upper- and lower-case letters, digits and at least one non-alphanumeric character aren't nearly as effective at helping users create passwords that are hard to crack, according to Microsoft Research scientist Stuart Schechter. Most people follow those rules by using a name or word they can remember and swapping out characters until the security requirements are met. Turning "password1" into "P@$$w0rd1" isn't a big improvement, however, according to Schechter. Hackers know the rules at least as well as users and routinely try common passwords using both the proper and leet-speak spelling that supposedly makes them "secure," he said. Predictability, and not the upper-caseness or symbol-ization of certain letters, is what makes passwords weak, so the best passwords are those the user can remember but hackers can't guess. Critiquing existing passwords and creating new, unguessable ones are the design goals behind Telepathwords, a site based largely on Schechter's work gathering and analyzing huge lists of passwords, "secret" questions and other authentication data that became public after major data breaches (including those at Facebook, Google, Yahoo, Twitter, LinkedIn and others included in a list of more than 2 million passwords stolen from 93,000 sites). The passwords were stolen using a keylogger contained in a virus that began collecting logins Oct. 21, and was stopped Nov. 24 after researchers at security firm TrustWave found millions of passwords on a server in the Netherlands. A comparison with lists of passwords stolen in 2006 showed that the 10 most common passwords made up almost three times as large a percentage in 2013 as in 2006. Comparing the result with previous breaches, Schechter found that during the seven years since a major breach at MySpace in 2006, passwords have gotten even more predictable. In 2006 the 10 most common passwords made up .9 percent of the total number of passwords discovered. By 2013 it had gone up to 2.4 percent. Telepathwords knows that, as well as what the most common passwords are, how often they turn up, all the alternative spellings, what the less-common passwords are and their spellings and everything else Schechter could find out about the way end users create, spell and re-use passwords. "We saw firsthand the tricks people use to construct passwords and then figured out which ones we should assume attackers also know,” Schechter said. Just avoiding the most common passwords or tricks to mis-spell them would make the average password more secure, but Telepathwords' goal is to make them unguessable, which it tries to do one letter at a time. "The system doesn’t ask the user to learn anything up-front or follow any specific rules," Schechter wrote in a blog announcing the site. "Rather, as you type each key of your intended password, it displays the characters it thinks you’re most likely to type next. If it succeeds in predicting one or more characters of the rest of your password, the evidence that these characters are predictable will be right in front of your eyes." The site doesn't actually provide new passwords. It just shows how predictable each letter of a current password is and suggests alternatives. The Telepathwords project site is available here. It went live Dec. 5. Image:Microsoft Corp.
New tool knows what makes passwords crackable and helps avoid them[/caption] Microsoft has posted a free online tool designed to check the security of passwords, or recommend more secure passwords that are also easier to type. Traditional rules requiring that "secure" passwords be case sensitive, include upper- and lower-case letters, digits and at least one non-alphanumeric character aren't nearly as effective at helping users create passwords that are hard to crack, according to Microsoft Research scientist Stuart Schechter. Most people follow those rules by using a name or word they can remember and swapping out characters until the security requirements are met. Turning "password1" into "P@$$w0rd1" isn't a big improvement, however, according to Schechter. Hackers know the rules at least as well as users and routinely try common passwords using both the proper and leet-speak spelling that supposedly makes them "secure," he said. Predictability, and not the upper-caseness or symbol-ization of certain letters, is what makes passwords weak, so the best passwords are those the user can remember but hackers can't guess. Critiquing existing passwords and creating new, unguessable ones are the design goals behind Telepathwords, a site based largely on Schechter's work gathering and analyzing huge lists of passwords, "secret" questions and other authentication data that became public after major data breaches (including those at Facebook, Google, Yahoo, Twitter, LinkedIn and others included in a list of more than 2 million passwords stolen from 93,000 sites). The passwords were stolen using a keylogger contained in a virus that began collecting logins Oct. 21, and was stopped Nov. 24 after researchers at security firm TrustWave found millions of passwords on a server in the Netherlands. A comparison with lists of passwords stolen in 2006 showed that the 10 most common passwords made up almost three times as large a percentage in 2013 as in 2006. Comparing the result with previous breaches, Schechter found that during the seven years since a major breach at MySpace in 2006, passwords have gotten even more predictable. In 2006 the 10 most common passwords made up .9 percent of the total number of passwords discovered. By 2013 it had gone up to 2.4 percent. Telepathwords knows that, as well as what the most common passwords are, how often they turn up, all the alternative spellings, what the less-common passwords are and their spellings and everything else Schechter could find out about the way end users create, spell and re-use passwords. "We saw firsthand the tricks people use to construct passwords and then figured out which ones we should assume attackers also know,” Schechter said. Just avoiding the most common passwords or tricks to mis-spell them would make the average password more secure, but Telepathwords' goal is to make them unguessable, which it tries to do one letter at a time. "The system doesn’t ask the user to learn anything up-front or follow any specific rules," Schechter wrote in a blog announcing the site. "Rather, as you type each key of your intended password, it displays the characters it thinks you’re most likely to type next. If it succeeds in predicting one or more characters of the rest of your password, the evidence that these characters are predictable will be right in front of your eyes." The site doesn't actually provide new passwords. It just shows how predictable each letter of a current password is and suggests alternatives. The Telepathwords project site is available here. It went live Dec. 5. Image:Microsoft Corp.
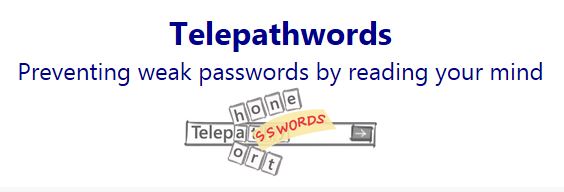 New tool knows what makes passwords crackable and helps avoid them[/caption] Microsoft has posted a free online tool designed to check the security of passwords, or recommend more secure passwords that are also easier to type. Traditional rules requiring that "secure" passwords be case sensitive, include upper- and lower-case letters, digits and at least one non-alphanumeric character aren't nearly as effective at helping users create passwords that are hard to crack, according to Microsoft Research scientist Stuart Schechter. Most people follow those rules by using a name or word they can remember and swapping out characters until the security requirements are met. Turning "password1" into "P@$$w0rd1" isn't a big improvement, however, according to Schechter. Hackers know the rules at least as well as users and routinely try common passwords using both the proper and leet-speak spelling that supposedly makes them "secure," he said. Predictability, and not the upper-caseness or symbol-ization of certain letters, is what makes passwords weak, so the best passwords are those the user can remember but hackers can't guess. Critiquing existing passwords and creating new, unguessable ones are the design goals behind Telepathwords, a site based largely on Schechter's work gathering and analyzing huge lists of passwords, "secret" questions and other authentication data that became public after major data breaches (including those at Facebook, Google, Yahoo, Twitter, LinkedIn and others included in a list of more than 2 million passwords stolen from 93,000 sites). The passwords were stolen using a keylogger contained in a virus that began collecting logins Oct. 21, and was stopped Nov. 24 after researchers at security firm TrustWave found millions of passwords on a server in the Netherlands. A comparison with lists of passwords stolen in 2006 showed that the 10 most common passwords made up almost three times as large a percentage in 2013 as in 2006. Comparing the result with previous breaches, Schechter found that during the seven years since a major breach at MySpace in 2006, passwords have gotten even more predictable. In 2006 the 10 most common passwords made up .9 percent of the total number of passwords discovered. By 2013 it had gone up to 2.4 percent. Telepathwords knows that, as well as what the most common passwords are, how often they turn up, all the alternative spellings, what the less-common passwords are and their spellings and everything else Schechter could find out about the way end users create, spell and re-use passwords. "We saw firsthand the tricks people use to construct passwords and then figured out which ones we should assume attackers also know,” Schechter said. Just avoiding the most common passwords or tricks to mis-spell them would make the average password more secure, but Telepathwords' goal is to make them unguessable, which it tries to do one letter at a time. "The system doesn’t ask the user to learn anything up-front or follow any specific rules," Schechter wrote in a blog announcing the site. "Rather, as you type each key of your intended password, it displays the characters it thinks you’re most likely to type next. If it succeeds in predicting one or more characters of the rest of your password, the evidence that these characters are predictable will be right in front of your eyes." The site doesn't actually provide new passwords. It just shows how predictable each letter of a current password is and suggests alternatives. The Telepathwords project site is available here. It went live Dec. 5. Image:Microsoft Corp.
New tool knows what makes passwords crackable and helps avoid them[/caption] Microsoft has posted a free online tool designed to check the security of passwords, or recommend more secure passwords that are also easier to type. Traditional rules requiring that "secure" passwords be case sensitive, include upper- and lower-case letters, digits and at least one non-alphanumeric character aren't nearly as effective at helping users create passwords that are hard to crack, according to Microsoft Research scientist Stuart Schechter. Most people follow those rules by using a name or word they can remember and swapping out characters until the security requirements are met. Turning "password1" into "P@$$w0rd1" isn't a big improvement, however, according to Schechter. Hackers know the rules at least as well as users and routinely try common passwords using both the proper and leet-speak spelling that supposedly makes them "secure," he said. Predictability, and not the upper-caseness or symbol-ization of certain letters, is what makes passwords weak, so the best passwords are those the user can remember but hackers can't guess. Critiquing existing passwords and creating new, unguessable ones are the design goals behind Telepathwords, a site based largely on Schechter's work gathering and analyzing huge lists of passwords, "secret" questions and other authentication data that became public after major data breaches (including those at Facebook, Google, Yahoo, Twitter, LinkedIn and others included in a list of more than 2 million passwords stolen from 93,000 sites). The passwords were stolen using a keylogger contained in a virus that began collecting logins Oct. 21, and was stopped Nov. 24 after researchers at security firm TrustWave found millions of passwords on a server in the Netherlands. A comparison with lists of passwords stolen in 2006 showed that the 10 most common passwords made up almost three times as large a percentage in 2013 as in 2006. Comparing the result with previous breaches, Schechter found that during the seven years since a major breach at MySpace in 2006, passwords have gotten even more predictable. In 2006 the 10 most common passwords made up .9 percent of the total number of passwords discovered. By 2013 it had gone up to 2.4 percent. Telepathwords knows that, as well as what the most common passwords are, how often they turn up, all the alternative spellings, what the less-common passwords are and their spellings and everything else Schechter could find out about the way end users create, spell and re-use passwords. "We saw firsthand the tricks people use to construct passwords and then figured out which ones we should assume attackers also know,” Schechter said. Just avoiding the most common passwords or tricks to mis-spell them would make the average password more secure, but Telepathwords' goal is to make them unguessable, which it tries to do one letter at a time. "The system doesn’t ask the user to learn anything up-front or follow any specific rules," Schechter wrote in a blog announcing the site. "Rather, as you type each key of your intended password, it displays the characters it thinks you’re most likely to type next. If it succeeds in predicting one or more characters of the rest of your password, the evidence that these characters are predictable will be right in front of your eyes." The site doesn't actually provide new passwords. It just shows how predictable each letter of a current password is and suggests alternatives. The Telepathwords project site is available here. It went live Dec. 5. Image:Microsoft Corp.