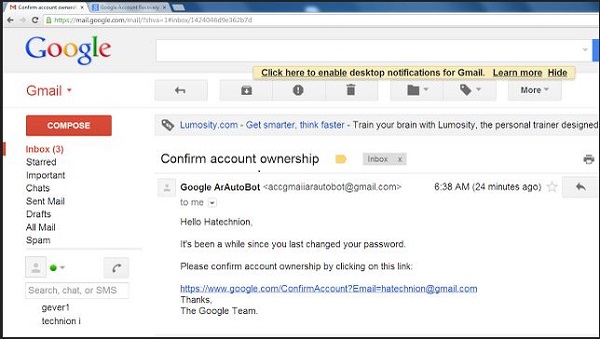
 Screen shot from Oren Hafif's proof-of-concept attack on Gmail flaws[/caption] Google is reporting it has fixed a bug in its password-reset system that would have allowed anyone able to spoof a reminder from Gmail to take over all a user's Google accounts and threaten any to which they're connected. The "high impact" security hole was identified Nov. 21 by security auditor and penetration tester Oren Hafif, who was testing the password-reset process on Gmail. The exploit would require spoofing a Gmail reminding users to reset their Gmail passwords, and include a link to a fake site on which to do it, but redirects the user to Google's real password-reset page. When the user clicks on the Password Reset button and logs into prove his/her identity, the attacker's website launches a cross-site scripting attack that captures the user's login information and the authentication cookie Google sets to allow access to the account. The exploit bypasses a series of steps designed to stop exactly that kind of attack, requiring the user to fill out CAPTCHA data and answer secret questions. With the password and authentication cookie in hand, however, the attacker is able to access and change the password on the Gmail account as well, taking control of all the user's Google accounts. The weaknesses (two of them, according to Ars Technica's Dan Goodin) revolved around Google's willingness to let web requests directed at it to be sent elsewhere. With the redirect working and the Google-provided authentication cookie in hand, Hafif was able to use XSS to re-visit the site and bypass additional security checks to avoid answering a long series of secret questions before being granted access. Hafif collected kudos from Reddit, and thanks from Google, though Google's thanks are posted on a Google+ account that requires logging in to Google to read about a highly effective exploit that takes advantage of people trying to log in to Google. Hafif also got a promise from Google of $5,100 under its bug-hunter program for reporting the flaws, and got himself another entry in Google's bug-hunter Hall of Fame. "Google security team acted really fast," Hafif wrote. Image: Google/Oren Hafif
Screen shot from Oren Hafif's proof-of-concept attack on Gmail flaws[/caption] Google is reporting it has fixed a bug in its password-reset system that would have allowed anyone able to spoof a reminder from Gmail to take over all a user's Google accounts and threaten any to which they're connected. The "high impact" security hole was identified Nov. 21 by security auditor and penetration tester Oren Hafif, who was testing the password-reset process on Gmail. The exploit would require spoofing a Gmail reminding users to reset their Gmail passwords, and include a link to a fake site on which to do it, but redirects the user to Google's real password-reset page. When the user clicks on the Password Reset button and logs into prove his/her identity, the attacker's website launches a cross-site scripting attack that captures the user's login information and the authentication cookie Google sets to allow access to the account. The exploit bypasses a series of steps designed to stop exactly that kind of attack, requiring the user to fill out CAPTCHA data and answer secret questions. With the password and authentication cookie in hand, however, the attacker is able to access and change the password on the Gmail account as well, taking control of all the user's Google accounts. The weaknesses (two of them, according to Ars Technica's Dan Goodin) revolved around Google's willingness to let web requests directed at it to be sent elsewhere. With the redirect working and the Google-provided authentication cookie in hand, Hafif was able to use XSS to re-visit the site and bypass additional security checks to avoid answering a long series of secret questions before being granted access. Hafif collected kudos from Reddit, and thanks from Google, though Google's thanks are posted on a Google+ account that requires logging in to Google to read about a highly effective exploit that takes advantage of people trying to log in to Google. Hafif also got a promise from Google of $5,100 under its bug-hunter program for reporting the flaws, and got himself another entry in Google's bug-hunter Hall of Fame. "Google security team acted really fast," Hafif wrote. Image: Google/Oren Hafif Bug-Hunter Gets $5K for 'High-Impact' Gmail Exploit
[caption id="attachment_14502" align="aligncenter" width="600"]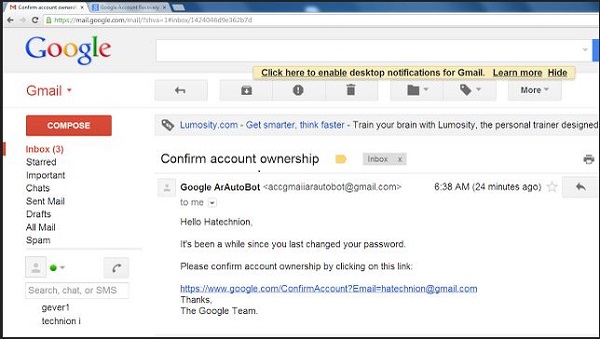 Screen shot from Oren Hafif's proof-of-concept attack on Gmail flaws[/caption] Google is reporting it has fixed a bug in its password-reset system that would have allowed anyone able to spoof a reminder from Gmail to take over all a user's Google accounts and threaten any to which they're connected. The "high impact" security hole was identified Nov. 21 by security auditor and penetration tester Oren Hafif, who was testing the password-reset process on Gmail. The exploit would require spoofing a Gmail reminding users to reset their Gmail passwords, and include a link to a fake site on which to do it, but redirects the user to Google's real password-reset page. When the user clicks on the Password Reset button and logs into prove his/her identity, the attacker's website launches a cross-site scripting attack that captures the user's login information and the authentication cookie Google sets to allow access to the account. The exploit bypasses a series of steps designed to stop exactly that kind of attack, requiring the user to fill out CAPTCHA data and answer secret questions. With the password and authentication cookie in hand, however, the attacker is able to access and change the password on the Gmail account as well, taking control of all the user's Google accounts. The weaknesses (two of them, according to Ars Technica's Dan Goodin) revolved around Google's willingness to let web requests directed at it to be sent elsewhere. With the redirect working and the Google-provided authentication cookie in hand, Hafif was able to use XSS to re-visit the site and bypass additional security checks to avoid answering a long series of secret questions before being granted access. Hafif collected kudos from Reddit, and thanks from Google, though Google's thanks are posted on a Google+ account that requires logging in to Google to read about a highly effective exploit that takes advantage of people trying to log in to Google. Hafif also got a promise from Google of $5,100 under its bug-hunter program for reporting the flaws, and got himself another entry in Google's bug-hunter Hall of Fame. "Google security team acted really fast," Hafif wrote. Image: Google/Oren Hafif
Screen shot from Oren Hafif's proof-of-concept attack on Gmail flaws[/caption] Google is reporting it has fixed a bug in its password-reset system that would have allowed anyone able to spoof a reminder from Gmail to take over all a user's Google accounts and threaten any to which they're connected. The "high impact" security hole was identified Nov. 21 by security auditor and penetration tester Oren Hafif, who was testing the password-reset process on Gmail. The exploit would require spoofing a Gmail reminding users to reset their Gmail passwords, and include a link to a fake site on which to do it, but redirects the user to Google's real password-reset page. When the user clicks on the Password Reset button and logs into prove his/her identity, the attacker's website launches a cross-site scripting attack that captures the user's login information and the authentication cookie Google sets to allow access to the account. The exploit bypasses a series of steps designed to stop exactly that kind of attack, requiring the user to fill out CAPTCHA data and answer secret questions. With the password and authentication cookie in hand, however, the attacker is able to access and change the password on the Gmail account as well, taking control of all the user's Google accounts. The weaknesses (two of them, according to Ars Technica's Dan Goodin) revolved around Google's willingness to let web requests directed at it to be sent elsewhere. With the redirect working and the Google-provided authentication cookie in hand, Hafif was able to use XSS to re-visit the site and bypass additional security checks to avoid answering a long series of secret questions before being granted access. Hafif collected kudos from Reddit, and thanks from Google, though Google's thanks are posted on a Google+ account that requires logging in to Google to read about a highly effective exploit that takes advantage of people trying to log in to Google. Hafif also got a promise from Google of $5,100 under its bug-hunter program for reporting the flaws, and got himself another entry in Google's bug-hunter Hall of Fame. "Google security team acted really fast," Hafif wrote. Image: Google/Oren Hafif
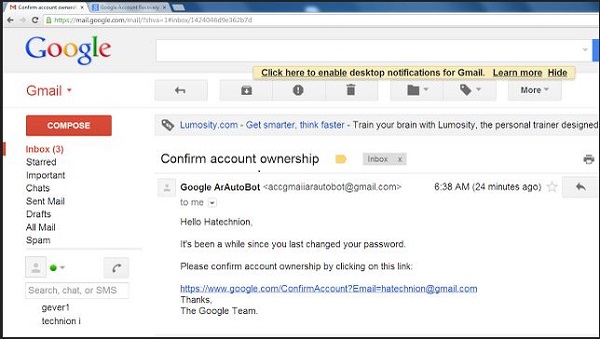 Screen shot from Oren Hafif's proof-of-concept attack on Gmail flaws[/caption] Google is reporting it has fixed a bug in its password-reset system that would have allowed anyone able to spoof a reminder from Gmail to take over all a user's Google accounts and threaten any to which they're connected. The "high impact" security hole was identified Nov. 21 by security auditor and penetration tester Oren Hafif, who was testing the password-reset process on Gmail. The exploit would require spoofing a Gmail reminding users to reset their Gmail passwords, and include a link to a fake site on which to do it, but redirects the user to Google's real password-reset page. When the user clicks on the Password Reset button and logs into prove his/her identity, the attacker's website launches a cross-site scripting attack that captures the user's login information and the authentication cookie Google sets to allow access to the account. The exploit bypasses a series of steps designed to stop exactly that kind of attack, requiring the user to fill out CAPTCHA data and answer secret questions. With the password and authentication cookie in hand, however, the attacker is able to access and change the password on the Gmail account as well, taking control of all the user's Google accounts. The weaknesses (two of them, according to Ars Technica's Dan Goodin) revolved around Google's willingness to let web requests directed at it to be sent elsewhere. With the redirect working and the Google-provided authentication cookie in hand, Hafif was able to use XSS to re-visit the site and bypass additional security checks to avoid answering a long series of secret questions before being granted access. Hafif collected kudos from Reddit, and thanks from Google, though Google's thanks are posted on a Google+ account that requires logging in to Google to read about a highly effective exploit that takes advantage of people trying to log in to Google. Hafif also got a promise from Google of $5,100 under its bug-hunter program for reporting the flaws, and got himself another entry in Google's bug-hunter Hall of Fame. "Google security team acted really fast," Hafif wrote. Image: Google/Oren Hafif
Screen shot from Oren Hafif's proof-of-concept attack on Gmail flaws[/caption] Google is reporting it has fixed a bug in its password-reset system that would have allowed anyone able to spoof a reminder from Gmail to take over all a user's Google accounts and threaten any to which they're connected. The "high impact" security hole was identified Nov. 21 by security auditor and penetration tester Oren Hafif, who was testing the password-reset process on Gmail. The exploit would require spoofing a Gmail reminding users to reset their Gmail passwords, and include a link to a fake site on which to do it, but redirects the user to Google's real password-reset page. When the user clicks on the Password Reset button and logs into prove his/her identity, the attacker's website launches a cross-site scripting attack that captures the user's login information and the authentication cookie Google sets to allow access to the account. The exploit bypasses a series of steps designed to stop exactly that kind of attack, requiring the user to fill out CAPTCHA data and answer secret questions. With the password and authentication cookie in hand, however, the attacker is able to access and change the password on the Gmail account as well, taking control of all the user's Google accounts. The weaknesses (two of them, according to Ars Technica's Dan Goodin) revolved around Google's willingness to let web requests directed at it to be sent elsewhere. With the redirect working and the Google-provided authentication cookie in hand, Hafif was able to use XSS to re-visit the site and bypass additional security checks to avoid answering a long series of secret questions before being granted access. Hafif collected kudos from Reddit, and thanks from Google, though Google's thanks are posted on a Google+ account that requires logging in to Google to read about a highly effective exploit that takes advantage of people trying to log in to Google. Hafif also got a promise from Google of $5,100 under its bug-hunter program for reporting the flaws, and got himself another entry in Google's bug-hunter Hall of Fame. "Google security team acted really fast," Hafif wrote. Image: Google/Oren Hafif