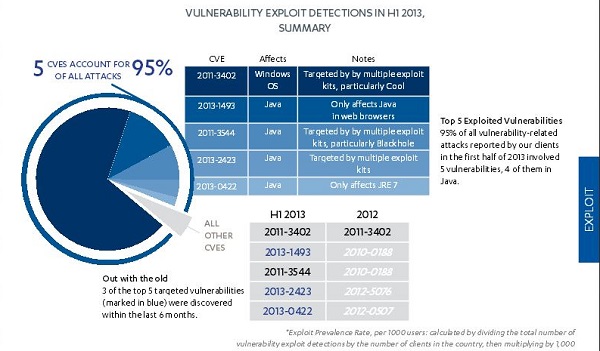
 Exploit attacks focus on Java[/caption] Java has replaced Windows as the top target for hackers within corporate IT infrastructures, according to a new threat report from security software developer F-Secure. Java has become so popular a target that it accounts for four of the five most-attacked security flaws in software used within corporate IT infrastructures. Organizations trying to reduce or eliminate malware, ransomware, backdoors, or Trojans can make a really good start by just shutting down Java within their own firewalls, according to the results of according to the most recent F-Secure Threat Report, which covers the first half of 2013. According to data F-Secure collected through the cloud-based telemetry service it provides for commercial clients, 95 percent of all exploit attacks focused on just five security flaws–four of which appear in either the Java browser plug-in or the Java Runtime Environment (JRE). The fifth (which accounts for 69 percent of all exploit attacks all by itself) is an exploit aimed at a Windows True Type Font vulnerability." Having a flaw to attack is only half the battle, however. Hackers also have to put an exploit in contact with a PC or server belonging to an organization on their target lists. Spear-phishing – aiming an e-mail with a malware-poisoned attachment at employees of a specific company or department – is still the most successful way to do that. The most successful type of document are those purporting to be about politics, corporate business or military issues, the report found. Of the top five vulnerabilities, three had been known publicly for less than six months, demonstrating a shift toward attacks based on unknown zero-day vulnerabilities, or those that had been announced and patched so recently that a large percentage of users can be counted on to still be vulnerable. During 2012, attacks focused mainly on flaws that had been known for some time, such as the Adobe Reader/Acrobat flaw known as CVE-2010-0288 that had been published two years earlier, according to the report. Attacks on Java accounted for half of all exploit attacks during 2013, up from one third of all exploit attacks during 2012. The increase (and Java's hold on spots 2, 3, 4 and 5 on the most-attacked-vulnerability list) isn't surprising, considering that Java is (according to the report) "probably" the second-most-common piece of software within corporate IT infrastructures. The factor that really pushed Java up on the exploit-target list, however, was publicity surrounding successful attacks on Facebook, Twitter, Apple and NBC that used Java weaknesses for their initial assault. In response, the Java-owning Oracle Corp. has issued a steady stream of security updates, raising the default security level to "High" and recommending that corporate security managers remove Java Runtime installations to the greatest degree possible. Lacking the ability to kill off the JRE, organizations should remove or disable the Java browser plug-in, "which is the first point of entry that exploits target to gain access to the program," the F-Secure report said. Companies for whom outright bans of Java are impractical can minimize their exposure by tightening Java security settings, "configuring web browser settings to minimize unwanted applet execution (or installing other third-party plug-ins to do so) and monitoring network traffic." Another contributing factor to both the increase in attacks and growing focus on a small number of vulnerabilities is the burgeoning commercial market for such exploits. Hackers creating successful exploits can often make more money selling the exploits to the highest bidder rather than having to do all the hacking themselves – especially if the exploit addresses a previously unknown flaw, the report found. The malware market is also consolidating onto commercial versions of the most-successful exploit software: 70 percent of all exploit attacks were launched using one of five exploit kits: BlackHole, SweetOrange, Crimeboss, Styx and Cool. The remaining 30 percent of attacks come from 28 separate kits. "The exploit kit development space has been highly active in the last few months, as we’ve observed at least one new (or revamped) exploit kit being created each month on average," F-Secure's data showed. "The top five kits are also undergoing active development, with their authors constantly adding new exploits targeting recently announced vulnerabilities." Image:F-Secure 1H 2013 Threat Report
Exploit attacks focus on Java[/caption] Java has replaced Windows as the top target for hackers within corporate IT infrastructures, according to a new threat report from security software developer F-Secure. Java has become so popular a target that it accounts for four of the five most-attacked security flaws in software used within corporate IT infrastructures. Organizations trying to reduce or eliminate malware, ransomware, backdoors, or Trojans can make a really good start by just shutting down Java within their own firewalls, according to the results of according to the most recent F-Secure Threat Report, which covers the first half of 2013. According to data F-Secure collected through the cloud-based telemetry service it provides for commercial clients, 95 percent of all exploit attacks focused on just five security flaws–four of which appear in either the Java browser plug-in or the Java Runtime Environment (JRE). The fifth (which accounts for 69 percent of all exploit attacks all by itself) is an exploit aimed at a Windows True Type Font vulnerability." Having a flaw to attack is only half the battle, however. Hackers also have to put an exploit in contact with a PC or server belonging to an organization on their target lists. Spear-phishing – aiming an e-mail with a malware-poisoned attachment at employees of a specific company or department – is still the most successful way to do that. The most successful type of document are those purporting to be about politics, corporate business or military issues, the report found. Of the top five vulnerabilities, three had been known publicly for less than six months, demonstrating a shift toward attacks based on unknown zero-day vulnerabilities, or those that had been announced and patched so recently that a large percentage of users can be counted on to still be vulnerable. During 2012, attacks focused mainly on flaws that had been known for some time, such as the Adobe Reader/Acrobat flaw known as CVE-2010-0288 that had been published two years earlier, according to the report. Attacks on Java accounted for half of all exploit attacks during 2013, up from one third of all exploit attacks during 2012. The increase (and Java's hold on spots 2, 3, 4 and 5 on the most-attacked-vulnerability list) isn't surprising, considering that Java is (according to the report) "probably" the second-most-common piece of software within corporate IT infrastructures. The factor that really pushed Java up on the exploit-target list, however, was publicity surrounding successful attacks on Facebook, Twitter, Apple and NBC that used Java weaknesses for their initial assault. In response, the Java-owning Oracle Corp. has issued a steady stream of security updates, raising the default security level to "High" and recommending that corporate security managers remove Java Runtime installations to the greatest degree possible. Lacking the ability to kill off the JRE, organizations should remove or disable the Java browser plug-in, "which is the first point of entry that exploits target to gain access to the program," the F-Secure report said. Companies for whom outright bans of Java are impractical can minimize their exposure by tightening Java security settings, "configuring web browser settings to minimize unwanted applet execution (or installing other third-party plug-ins to do so) and monitoring network traffic." Another contributing factor to both the increase in attacks and growing focus on a small number of vulnerabilities is the burgeoning commercial market for such exploits. Hackers creating successful exploits can often make more money selling the exploits to the highest bidder rather than having to do all the hacking themselves – especially if the exploit addresses a previously unknown flaw, the report found. The malware market is also consolidating onto commercial versions of the most-successful exploit software: 70 percent of all exploit attacks were launched using one of five exploit kits: BlackHole, SweetOrange, Crimeboss, Styx and Cool. The remaining 30 percent of attacks come from 28 separate kits. "The exploit kit development space has been highly active in the last few months, as we’ve observed at least one new (or revamped) exploit kit being created each month on average," F-Secure's data showed. "The top five kits are also undergoing active development, with their authors constantly adding new exploits targeting recently announced vulnerabilities." Image:F-Secure 1H 2013 Threat Report Best Datacenter Defense Against Malware: Turn Off Java
[caption id="attachment_12577" align="aligncenter" width="600"]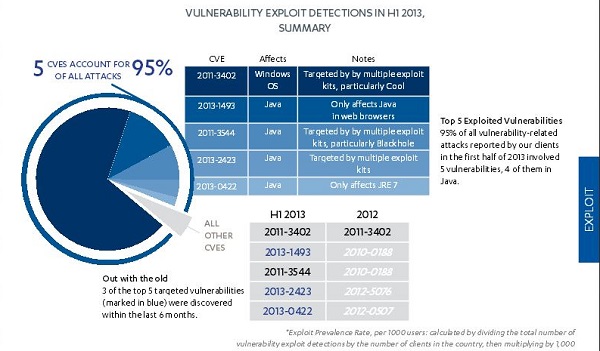 Exploit attacks focus on Java[/caption] Java has replaced Windows as the top target for hackers within corporate IT infrastructures, according to a new threat report from security software developer F-Secure. Java has become so popular a target that it accounts for four of the five most-attacked security flaws in software used within corporate IT infrastructures. Organizations trying to reduce or eliminate malware, ransomware, backdoors, or Trojans can make a really good start by just shutting down Java within their own firewalls, according to the results of according to the most recent F-Secure Threat Report, which covers the first half of 2013. According to data F-Secure collected through the cloud-based telemetry service it provides for commercial clients, 95 percent of all exploit attacks focused on just five security flaws–four of which appear in either the Java browser plug-in or the Java Runtime Environment (JRE). The fifth (which accounts for 69 percent of all exploit attacks all by itself) is an exploit aimed at a Windows True Type Font vulnerability." Having a flaw to attack is only half the battle, however. Hackers also have to put an exploit in contact with a PC or server belonging to an organization on their target lists. Spear-phishing – aiming an e-mail with a malware-poisoned attachment at employees of a specific company or department – is still the most successful way to do that. The most successful type of document are those purporting to be about politics, corporate business or military issues, the report found. Of the top five vulnerabilities, three had been known publicly for less than six months, demonstrating a shift toward attacks based on unknown zero-day vulnerabilities, or those that had been announced and patched so recently that a large percentage of users can be counted on to still be vulnerable. During 2012, attacks focused mainly on flaws that had been known for some time, such as the Adobe Reader/Acrobat flaw known as CVE-2010-0288 that had been published two years earlier, according to the report. Attacks on Java accounted for half of all exploit attacks during 2013, up from one third of all exploit attacks during 2012. The increase (and Java's hold on spots 2, 3, 4 and 5 on the most-attacked-vulnerability list) isn't surprising, considering that Java is (according to the report) "probably" the second-most-common piece of software within corporate IT infrastructures. The factor that really pushed Java up on the exploit-target list, however, was publicity surrounding successful attacks on Facebook, Twitter, Apple and NBC that used Java weaknesses for their initial assault. In response, the Java-owning Oracle Corp. has issued a steady stream of security updates, raising the default security level to "High" and recommending that corporate security managers remove Java Runtime installations to the greatest degree possible. Lacking the ability to kill off the JRE, organizations should remove or disable the Java browser plug-in, "which is the first point of entry that exploits target to gain access to the program," the F-Secure report said. Companies for whom outright bans of Java are impractical can minimize their exposure by tightening Java security settings, "configuring web browser settings to minimize unwanted applet execution (or installing other third-party plug-ins to do so) and monitoring network traffic." Another contributing factor to both the increase in attacks and growing focus on a small number of vulnerabilities is the burgeoning commercial market for such exploits. Hackers creating successful exploits can often make more money selling the exploits to the highest bidder rather than having to do all the hacking themselves – especially if the exploit addresses a previously unknown flaw, the report found. The malware market is also consolidating onto commercial versions of the most-successful exploit software: 70 percent of all exploit attacks were launched using one of five exploit kits: BlackHole, SweetOrange, Crimeboss, Styx and Cool. The remaining 30 percent of attacks come from 28 separate kits. "The exploit kit development space has been highly active in the last few months, as we’ve observed at least one new (or revamped) exploit kit being created each month on average," F-Secure's data showed. "The top five kits are also undergoing active development, with their authors constantly adding new exploits targeting recently announced vulnerabilities." Image:F-Secure 1H 2013 Threat Report
Exploit attacks focus on Java[/caption] Java has replaced Windows as the top target for hackers within corporate IT infrastructures, according to a new threat report from security software developer F-Secure. Java has become so popular a target that it accounts for four of the five most-attacked security flaws in software used within corporate IT infrastructures. Organizations trying to reduce or eliminate malware, ransomware, backdoors, or Trojans can make a really good start by just shutting down Java within their own firewalls, according to the results of according to the most recent F-Secure Threat Report, which covers the first half of 2013. According to data F-Secure collected through the cloud-based telemetry service it provides for commercial clients, 95 percent of all exploit attacks focused on just five security flaws–four of which appear in either the Java browser plug-in or the Java Runtime Environment (JRE). The fifth (which accounts for 69 percent of all exploit attacks all by itself) is an exploit aimed at a Windows True Type Font vulnerability." Having a flaw to attack is only half the battle, however. Hackers also have to put an exploit in contact with a PC or server belonging to an organization on their target lists. Spear-phishing – aiming an e-mail with a malware-poisoned attachment at employees of a specific company or department – is still the most successful way to do that. The most successful type of document are those purporting to be about politics, corporate business or military issues, the report found. Of the top five vulnerabilities, three had been known publicly for less than six months, demonstrating a shift toward attacks based on unknown zero-day vulnerabilities, or those that had been announced and patched so recently that a large percentage of users can be counted on to still be vulnerable. During 2012, attacks focused mainly on flaws that had been known for some time, such as the Adobe Reader/Acrobat flaw known as CVE-2010-0288 that had been published two years earlier, according to the report. Attacks on Java accounted for half of all exploit attacks during 2013, up from one third of all exploit attacks during 2012. The increase (and Java's hold on spots 2, 3, 4 and 5 on the most-attacked-vulnerability list) isn't surprising, considering that Java is (according to the report) "probably" the second-most-common piece of software within corporate IT infrastructures. The factor that really pushed Java up on the exploit-target list, however, was publicity surrounding successful attacks on Facebook, Twitter, Apple and NBC that used Java weaknesses for their initial assault. In response, the Java-owning Oracle Corp. has issued a steady stream of security updates, raising the default security level to "High" and recommending that corporate security managers remove Java Runtime installations to the greatest degree possible. Lacking the ability to kill off the JRE, organizations should remove or disable the Java browser plug-in, "which is the first point of entry that exploits target to gain access to the program," the F-Secure report said. Companies for whom outright bans of Java are impractical can minimize their exposure by tightening Java security settings, "configuring web browser settings to minimize unwanted applet execution (or installing other third-party plug-ins to do so) and monitoring network traffic." Another contributing factor to both the increase in attacks and growing focus on a small number of vulnerabilities is the burgeoning commercial market for such exploits. Hackers creating successful exploits can often make more money selling the exploits to the highest bidder rather than having to do all the hacking themselves – especially if the exploit addresses a previously unknown flaw, the report found. The malware market is also consolidating onto commercial versions of the most-successful exploit software: 70 percent of all exploit attacks were launched using one of five exploit kits: BlackHole, SweetOrange, Crimeboss, Styx and Cool. The remaining 30 percent of attacks come from 28 separate kits. "The exploit kit development space has been highly active in the last few months, as we’ve observed at least one new (or revamped) exploit kit being created each month on average," F-Secure's data showed. "The top five kits are also undergoing active development, with their authors constantly adding new exploits targeting recently announced vulnerabilities." Image:F-Secure 1H 2013 Threat Report
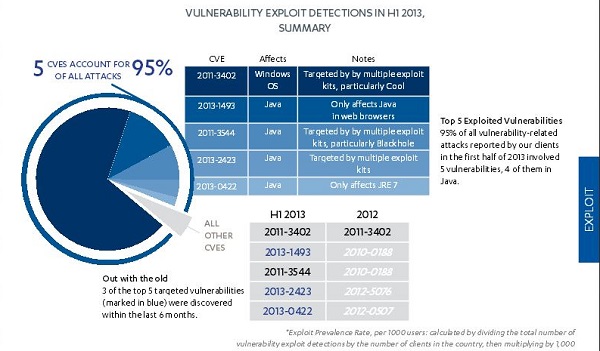 Exploit attacks focus on Java[/caption] Java has replaced Windows as the top target for hackers within corporate IT infrastructures, according to a new threat report from security software developer F-Secure. Java has become so popular a target that it accounts for four of the five most-attacked security flaws in software used within corporate IT infrastructures. Organizations trying to reduce or eliminate malware, ransomware, backdoors, or Trojans can make a really good start by just shutting down Java within their own firewalls, according to the results of according to the most recent F-Secure Threat Report, which covers the first half of 2013. According to data F-Secure collected through the cloud-based telemetry service it provides for commercial clients, 95 percent of all exploit attacks focused on just five security flaws–four of which appear in either the Java browser plug-in or the Java Runtime Environment (JRE). The fifth (which accounts for 69 percent of all exploit attacks all by itself) is an exploit aimed at a Windows True Type Font vulnerability." Having a flaw to attack is only half the battle, however. Hackers also have to put an exploit in contact with a PC or server belonging to an organization on their target lists. Spear-phishing – aiming an e-mail with a malware-poisoned attachment at employees of a specific company or department – is still the most successful way to do that. The most successful type of document are those purporting to be about politics, corporate business or military issues, the report found. Of the top five vulnerabilities, three had been known publicly for less than six months, demonstrating a shift toward attacks based on unknown zero-day vulnerabilities, or those that had been announced and patched so recently that a large percentage of users can be counted on to still be vulnerable. During 2012, attacks focused mainly on flaws that had been known for some time, such as the Adobe Reader/Acrobat flaw known as CVE-2010-0288 that had been published two years earlier, according to the report. Attacks on Java accounted for half of all exploit attacks during 2013, up from one third of all exploit attacks during 2012. The increase (and Java's hold on spots 2, 3, 4 and 5 on the most-attacked-vulnerability list) isn't surprising, considering that Java is (according to the report) "probably" the second-most-common piece of software within corporate IT infrastructures. The factor that really pushed Java up on the exploit-target list, however, was publicity surrounding successful attacks on Facebook, Twitter, Apple and NBC that used Java weaknesses for their initial assault. In response, the Java-owning Oracle Corp. has issued a steady stream of security updates, raising the default security level to "High" and recommending that corporate security managers remove Java Runtime installations to the greatest degree possible. Lacking the ability to kill off the JRE, organizations should remove or disable the Java browser plug-in, "which is the first point of entry that exploits target to gain access to the program," the F-Secure report said. Companies for whom outright bans of Java are impractical can minimize their exposure by tightening Java security settings, "configuring web browser settings to minimize unwanted applet execution (or installing other third-party plug-ins to do so) and monitoring network traffic." Another contributing factor to both the increase in attacks and growing focus on a small number of vulnerabilities is the burgeoning commercial market for such exploits. Hackers creating successful exploits can often make more money selling the exploits to the highest bidder rather than having to do all the hacking themselves – especially if the exploit addresses a previously unknown flaw, the report found. The malware market is also consolidating onto commercial versions of the most-successful exploit software: 70 percent of all exploit attacks were launched using one of five exploit kits: BlackHole, SweetOrange, Crimeboss, Styx and Cool. The remaining 30 percent of attacks come from 28 separate kits. "The exploit kit development space has been highly active in the last few months, as we’ve observed at least one new (or revamped) exploit kit being created each month on average," F-Secure's data showed. "The top five kits are also undergoing active development, with their authors constantly adding new exploits targeting recently announced vulnerabilities." Image:F-Secure 1H 2013 Threat Report
Exploit attacks focus on Java[/caption] Java has replaced Windows as the top target for hackers within corporate IT infrastructures, according to a new threat report from security software developer F-Secure. Java has become so popular a target that it accounts for four of the five most-attacked security flaws in software used within corporate IT infrastructures. Organizations trying to reduce or eliminate malware, ransomware, backdoors, or Trojans can make a really good start by just shutting down Java within their own firewalls, according to the results of according to the most recent F-Secure Threat Report, which covers the first half of 2013. According to data F-Secure collected through the cloud-based telemetry service it provides for commercial clients, 95 percent of all exploit attacks focused on just five security flaws–four of which appear in either the Java browser plug-in or the Java Runtime Environment (JRE). The fifth (which accounts for 69 percent of all exploit attacks all by itself) is an exploit aimed at a Windows True Type Font vulnerability." Having a flaw to attack is only half the battle, however. Hackers also have to put an exploit in contact with a PC or server belonging to an organization on their target lists. Spear-phishing – aiming an e-mail with a malware-poisoned attachment at employees of a specific company or department – is still the most successful way to do that. The most successful type of document are those purporting to be about politics, corporate business or military issues, the report found. Of the top five vulnerabilities, three had been known publicly for less than six months, demonstrating a shift toward attacks based on unknown zero-day vulnerabilities, or those that had been announced and patched so recently that a large percentage of users can be counted on to still be vulnerable. During 2012, attacks focused mainly on flaws that had been known for some time, such as the Adobe Reader/Acrobat flaw known as CVE-2010-0288 that had been published two years earlier, according to the report. Attacks on Java accounted for half of all exploit attacks during 2013, up from one third of all exploit attacks during 2012. The increase (and Java's hold on spots 2, 3, 4 and 5 on the most-attacked-vulnerability list) isn't surprising, considering that Java is (according to the report) "probably" the second-most-common piece of software within corporate IT infrastructures. The factor that really pushed Java up on the exploit-target list, however, was publicity surrounding successful attacks on Facebook, Twitter, Apple and NBC that used Java weaknesses for their initial assault. In response, the Java-owning Oracle Corp. has issued a steady stream of security updates, raising the default security level to "High" and recommending that corporate security managers remove Java Runtime installations to the greatest degree possible. Lacking the ability to kill off the JRE, organizations should remove or disable the Java browser plug-in, "which is the first point of entry that exploits target to gain access to the program," the F-Secure report said. Companies for whom outright bans of Java are impractical can minimize their exposure by tightening Java security settings, "configuring web browser settings to minimize unwanted applet execution (or installing other third-party plug-ins to do so) and monitoring network traffic." Another contributing factor to both the increase in attacks and growing focus on a small number of vulnerabilities is the burgeoning commercial market for such exploits. Hackers creating successful exploits can often make more money selling the exploits to the highest bidder rather than having to do all the hacking themselves – especially if the exploit addresses a previously unknown flaw, the report found. The malware market is also consolidating onto commercial versions of the most-successful exploit software: 70 percent of all exploit attacks were launched using one of five exploit kits: BlackHole, SweetOrange, Crimeboss, Styx and Cool. The remaining 30 percent of attacks come from 28 separate kits. "The exploit kit development space has been highly active in the last few months, as we’ve observed at least one new (or revamped) exploit kit being created each month on average," F-Secure's data showed. "The top five kits are also undergoing active development, with their authors constantly adding new exploits targeting recently announced vulnerabilities." Image:F-Secure 1H 2013 Threat Report