It's just over 22 years since the first SIM (Subscriber Identity Module) cards appeared and now they're everywhere in cell phones and other mobile devices. They're mandatory in GSM devices. And now it's been revealed that some older SIM cards have a serious vulnerability that could affect 500 to 750 million cell phones out of the estimated 6 billion in use worldwide. Or maybe more, since satellite phones also use SIM cards.

The vulnerability was discovered by German security expert Karsten Nohl, who broke the encryption used by most cell phone carriers four years ago, allowing him to listen into phone calls. This vulnerability allows access to the software running on the SIM card. Nohl sent a fake message that exploits the weaker form of encryption used in older cards. In some 25 percent of his tests, the phones revealed the 56 bit
DES security key. Using this key, the phone could then be tricked with a follow up SMS message containing a virus that accessed the software, making the unthinkable possible: The SIM can be cloned or payment credentials can be copied. Similar silent update messages are used by phone operators to make configuration changes or upload new apps.

What's inside a SIM Card?
Most modern cards are based on the Java Card design, which is meant to be secure and portable. Applets are written in a cut-down version of Java and run in a limited memory environment. It uses a version of the
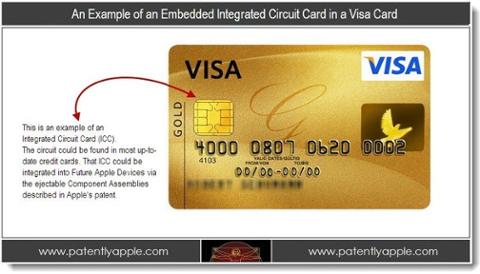
JVM called the Java Card Virtual Machine and a library which mitigates differences between various card hardware. All cards have a CPU, a fixed ROM and a reprogrammable (EEPROM), and a small amount of RAM, typically between 1K and 8K. The fixed ROM holds the OS and applets while the EEPROM contains rewriteable data such as contact details, network identifiers, SMS settings, etc. I'm surmising that it also holds patches or updated applets. So a SIM card is really just a very small CPU with RAM and ROM. It's more than powerful enough for the 128-bit encryption that's used to authenticate the phone. Though SIM cards come in many sizes, they are just different form factors -- they all do the same thing. And they're not just limited to phones. Credit cards contain the same processors as SIM cards, but so far no mention has been made as to whether they're as vulnerable. Given that banks reissue cards every couple of years, it's hopefully not the case. But who knows?
Security
Java has gotten bad rap this year through its use in browsers and various exploits that have had even the White House advise people to remove it. In this case though, it's not Java to blame but the continued use of an outdated encryption scheme. The 56-bit DES. was
cracked back in 1997. Moore's Law has CPUs doubling in transistor density every two years and doubling in performance every 18 months. So a 2013 CPU is at least 500 times as powerful as one from 1997. Add to this the increased processing capability available using the graphical processor unit in video cards, and it's clear that continuing to use DES. was a ticking time bomb. Modern SIM cards use the secure AES or Triple DES encryption methods, but according to Nohl's research many older ones are still in use.
 The vulnerability was discovered by German security expert Karsten Nohl, who broke the encryption used by most cell phone carriers four years ago, allowing him to listen into phone calls. This vulnerability allows access to the software running on the SIM card. Nohl sent a fake message that exploits the weaker form of encryption used in older cards. In some 25 percent of his tests, the phones revealed the 56 bit DES security key. Using this key, the phone could then be tricked with a follow up SMS message containing a virus that accessed the software, making the unthinkable possible: The SIM can be cloned or payment credentials can be copied. Similar silent update messages are used by phone operators to make configuration changes or upload new apps.
The vulnerability was discovered by German security expert Karsten Nohl, who broke the encryption used by most cell phone carriers four years ago, allowing him to listen into phone calls. This vulnerability allows access to the software running on the SIM card. Nohl sent a fake message that exploits the weaker form of encryption used in older cards. In some 25 percent of his tests, the phones revealed the 56 bit DES security key. Using this key, the phone could then be tricked with a follow up SMS message containing a virus that accessed the software, making the unthinkable possible: The SIM can be cloned or payment credentials can be copied. Similar silent update messages are used by phone operators to make configuration changes or upload new apps. 

![Go to article Objective C, Java Skills Needed for Mobile Dev [Guest Post]](/binaries/small/content/gallery/dice/insights/2011/10/fastmobileapps.jpg)