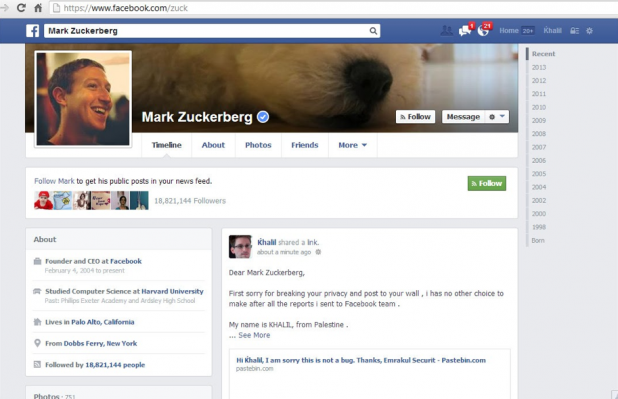
 Zuckerberg's Facebook wall, hacked.[/caption] Pop quiz for any security researchers out there: What’s the best way to draw Facebook’s attention to a bug that allows users to post messages on strangers’ walls? If you’re self-described security researcher Khalil Shreateh, the answer is: “Post a message about it on Mark Zuckerberg’s Facebook wall.” Shreateh doesn’t know Zuckerberg, but he used the bug to announce his findings right on the Facebook CEO’s timeline. Facebook, of course, reacted to Shreateh’s little stunt by disabling his account; minutes later, a company security engineer reached out to him, demanding the inner workings of the exploit. Which is funny, because Shreateh had already reached out to Facebook’s security team about the issue, via the Facebook Whitehat URL. When that didn’t work (“I don’t see anything when I click on the link except an error,” a Facebook security employee wrote back, according to Shreateh’s Website), he used the exploit to post a message onto the Facebook page of Sarah Goodin, a friend of Zuckerberg’s and one of the first people to create an account on the social network in Ye Olden Days. “Facebook security replay was that the link gives error opening,” Shreateh wrote on his blog, referring to the Facebook security employee’s earlier email. “If course they didnt use their authority to view sarah's privacy posts as sarah share her timeline posts with her friends only, i was able to view that post cause i'am the one who did post it even i'am not in her friend list.” After Facebook security refused to listen to him again (“I am sorry, this is not a bug,” they wrote back), Shreateh felt he had “no choice” but to post directly to Zuckerberg’s timeline. The response to that, of course, was immediate. “Unfortunately your report to our Whitehat system did not have enough technical information for us to take action on it,” Facebook reportedly wrote to him. “We cannot respond to reports which do not contain enough detail to allow us to reproduce an issue.” Facebook also refused to pay him the customary fee awarded to those who discover system bugs, as his use of the exploit apparently violated the social network’s Terms of Service (ToS). In an August 19 posting on Hacker News, a Facebook security team member suggested that the bug had been fixed late last week. “We get hundreds of reports every day,” this person wrote. “Many of our best reports come from people whose English isn't great—though this can be challenging, it's something we work with just fine and we have paid out over $1 million to hundreds of reporters.” Because Shreateh used the bug to exploit real users without their consent, the team member continued, he violated the ToS and is thus ineligible for payment: “We welcome and will pay out for future reports from him (and anyone else!) if they're found and demonstrated within these guidelines.” Let that be a lesson to any white-hat hackers out there: targeting Mark Zuckerberg will get Facebook’s attention, but probably not in the way you originally intended. Image: Khalil Shreateh
Zuckerberg's Facebook wall, hacked.[/caption] Pop quiz for any security researchers out there: What’s the best way to draw Facebook’s attention to a bug that allows users to post messages on strangers’ walls? If you’re self-described security researcher Khalil Shreateh, the answer is: “Post a message about it on Mark Zuckerberg’s Facebook wall.” Shreateh doesn’t know Zuckerberg, but he used the bug to announce his findings right on the Facebook CEO’s timeline. Facebook, of course, reacted to Shreateh’s little stunt by disabling his account; minutes later, a company security engineer reached out to him, demanding the inner workings of the exploit. Which is funny, because Shreateh had already reached out to Facebook’s security team about the issue, via the Facebook Whitehat URL. When that didn’t work (“I don’t see anything when I click on the link except an error,” a Facebook security employee wrote back, according to Shreateh’s Website), he used the exploit to post a message onto the Facebook page of Sarah Goodin, a friend of Zuckerberg’s and one of the first people to create an account on the social network in Ye Olden Days. “Facebook security replay was that the link gives error opening,” Shreateh wrote on his blog, referring to the Facebook security employee’s earlier email. “If course they didnt use their authority to view sarah's privacy posts as sarah share her timeline posts with her friends only, i was able to view that post cause i'am the one who did post it even i'am not in her friend list.” After Facebook security refused to listen to him again (“I am sorry, this is not a bug,” they wrote back), Shreateh felt he had “no choice” but to post directly to Zuckerberg’s timeline. The response to that, of course, was immediate. “Unfortunately your report to our Whitehat system did not have enough technical information for us to take action on it,” Facebook reportedly wrote to him. “We cannot respond to reports which do not contain enough detail to allow us to reproduce an issue.” Facebook also refused to pay him the customary fee awarded to those who discover system bugs, as his use of the exploit apparently violated the social network’s Terms of Service (ToS). In an August 19 posting on Hacker News, a Facebook security team member suggested that the bug had been fixed late last week. “We get hundreds of reports every day,” this person wrote. “Many of our best reports come from people whose English isn't great—though this can be challenging, it's something we work with just fine and we have paid out over $1 million to hundreds of reporters.” Because Shreateh used the bug to exploit real users without their consent, the team member continued, he violated the ToS and is thus ineligible for payment: “We welcome and will pay out for future reports from him (and anyone else!) if they're found and demonstrated within these guidelines.” Let that be a lesson to any white-hat hackers out there: targeting Mark Zuckerberg will get Facebook’s attention, but probably not in the way you originally intended. Image: Khalil Shreateh Hacking Zuckerberg Gets Facebook’s Attention
[caption id="attachment_11657" align="aligncenter" width="618"] 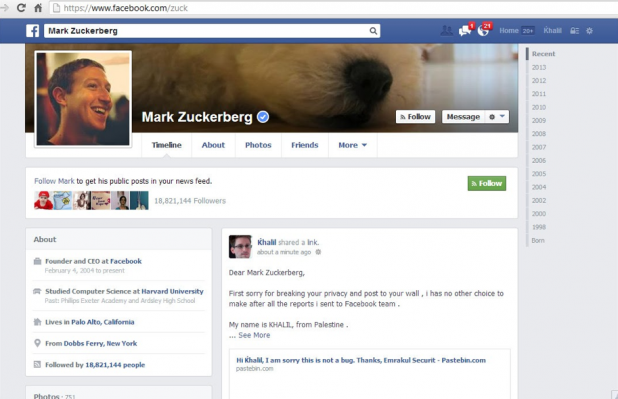 Zuckerberg's Facebook wall, hacked.[/caption] Pop quiz for any security researchers out there: What’s the best way to draw Facebook’s attention to a bug that allows users to post messages on strangers’ walls? If you’re self-described security researcher Khalil Shreateh, the answer is: “Post a message about it on Mark Zuckerberg’s Facebook wall.” Shreateh doesn’t know Zuckerberg, but he used the bug to announce his findings right on the Facebook CEO’s timeline. Facebook, of course, reacted to Shreateh’s little stunt by disabling his account; minutes later, a company security engineer reached out to him, demanding the inner workings of the exploit. Which is funny, because Shreateh had already reached out to Facebook’s security team about the issue, via the Facebook Whitehat URL. When that didn’t work (“I don’t see anything when I click on the link except an error,” a Facebook security employee wrote back, according to Shreateh’s Website), he used the exploit to post a message onto the Facebook page of Sarah Goodin, a friend of Zuckerberg’s and one of the first people to create an account on the social network in Ye Olden Days. “Facebook security replay was that the link gives error opening,” Shreateh wrote on his blog, referring to the Facebook security employee’s earlier email. “If course they didnt use their authority to view sarah's privacy posts as sarah share her timeline posts with her friends only, i was able to view that post cause i'am the one who did post it even i'am not in her friend list.” After Facebook security refused to listen to him again (“I am sorry, this is not a bug,” they wrote back), Shreateh felt he had “no choice” but to post directly to Zuckerberg’s timeline. The response to that, of course, was immediate. “Unfortunately your report to our Whitehat system did not have enough technical information for us to take action on it,” Facebook reportedly wrote to him. “We cannot respond to reports which do not contain enough detail to allow us to reproduce an issue.” Facebook also refused to pay him the customary fee awarded to those who discover system bugs, as his use of the exploit apparently violated the social network’s Terms of Service (ToS). In an August 19 posting on Hacker News, a Facebook security team member suggested that the bug had been fixed late last week. “We get hundreds of reports every day,” this person wrote. “Many of our best reports come from people whose English isn't great—though this can be challenging, it's something we work with just fine and we have paid out over $1 million to hundreds of reporters.” Because Shreateh used the bug to exploit real users without their consent, the team member continued, he violated the ToS and is thus ineligible for payment: “We welcome and will pay out for future reports from him (and anyone else!) if they're found and demonstrated within these guidelines.” Let that be a lesson to any white-hat hackers out there: targeting Mark Zuckerberg will get Facebook’s attention, but probably not in the way you originally intended. Image: Khalil Shreateh
Zuckerberg's Facebook wall, hacked.[/caption] Pop quiz for any security researchers out there: What’s the best way to draw Facebook’s attention to a bug that allows users to post messages on strangers’ walls? If you’re self-described security researcher Khalil Shreateh, the answer is: “Post a message about it on Mark Zuckerberg’s Facebook wall.” Shreateh doesn’t know Zuckerberg, but he used the bug to announce his findings right on the Facebook CEO’s timeline. Facebook, of course, reacted to Shreateh’s little stunt by disabling his account; minutes later, a company security engineer reached out to him, demanding the inner workings of the exploit. Which is funny, because Shreateh had already reached out to Facebook’s security team about the issue, via the Facebook Whitehat URL. When that didn’t work (“I don’t see anything when I click on the link except an error,” a Facebook security employee wrote back, according to Shreateh’s Website), he used the exploit to post a message onto the Facebook page of Sarah Goodin, a friend of Zuckerberg’s and one of the first people to create an account on the social network in Ye Olden Days. “Facebook security replay was that the link gives error opening,” Shreateh wrote on his blog, referring to the Facebook security employee’s earlier email. “If course they didnt use their authority to view sarah's privacy posts as sarah share her timeline posts with her friends only, i was able to view that post cause i'am the one who did post it even i'am not in her friend list.” After Facebook security refused to listen to him again (“I am sorry, this is not a bug,” they wrote back), Shreateh felt he had “no choice” but to post directly to Zuckerberg’s timeline. The response to that, of course, was immediate. “Unfortunately your report to our Whitehat system did not have enough technical information for us to take action on it,” Facebook reportedly wrote to him. “We cannot respond to reports which do not contain enough detail to allow us to reproduce an issue.” Facebook also refused to pay him the customary fee awarded to those who discover system bugs, as his use of the exploit apparently violated the social network’s Terms of Service (ToS). In an August 19 posting on Hacker News, a Facebook security team member suggested that the bug had been fixed late last week. “We get hundreds of reports every day,” this person wrote. “Many of our best reports come from people whose English isn't great—though this can be challenging, it's something we work with just fine and we have paid out over $1 million to hundreds of reporters.” Because Shreateh used the bug to exploit real users without their consent, the team member continued, he violated the ToS and is thus ineligible for payment: “We welcome and will pay out for future reports from him (and anyone else!) if they're found and demonstrated within these guidelines.” Let that be a lesson to any white-hat hackers out there: targeting Mark Zuckerberg will get Facebook’s attention, but probably not in the way you originally intended. Image: Khalil Shreateh
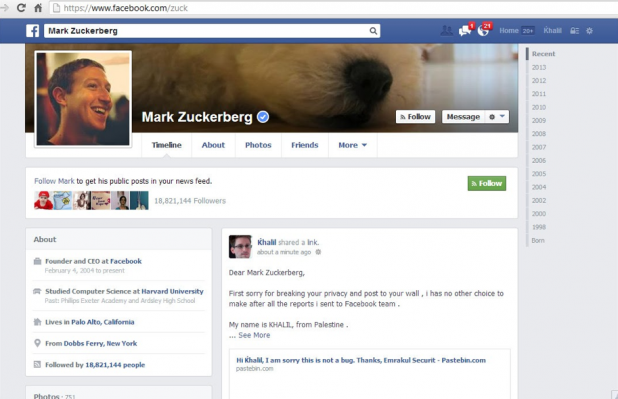 Zuckerberg's Facebook wall, hacked.[/caption] Pop quiz for any security researchers out there: What’s the best way to draw Facebook’s attention to a bug that allows users to post messages on strangers’ walls? If you’re self-described security researcher Khalil Shreateh, the answer is: “Post a message about it on Mark Zuckerberg’s Facebook wall.” Shreateh doesn’t know Zuckerberg, but he used the bug to announce his findings right on the Facebook CEO’s timeline. Facebook, of course, reacted to Shreateh’s little stunt by disabling his account; minutes later, a company security engineer reached out to him, demanding the inner workings of the exploit. Which is funny, because Shreateh had already reached out to Facebook’s security team about the issue, via the Facebook Whitehat URL. When that didn’t work (“I don’t see anything when I click on the link except an error,” a Facebook security employee wrote back, according to Shreateh’s Website), he used the exploit to post a message onto the Facebook page of Sarah Goodin, a friend of Zuckerberg’s and one of the first people to create an account on the social network in Ye Olden Days. “Facebook security replay was that the link gives error opening,” Shreateh wrote on his blog, referring to the Facebook security employee’s earlier email. “If course they didnt use their authority to view sarah's privacy posts as sarah share her timeline posts with her friends only, i was able to view that post cause i'am the one who did post it even i'am not in her friend list.” After Facebook security refused to listen to him again (“I am sorry, this is not a bug,” they wrote back), Shreateh felt he had “no choice” but to post directly to Zuckerberg’s timeline. The response to that, of course, was immediate. “Unfortunately your report to our Whitehat system did not have enough technical information for us to take action on it,” Facebook reportedly wrote to him. “We cannot respond to reports which do not contain enough detail to allow us to reproduce an issue.” Facebook also refused to pay him the customary fee awarded to those who discover system bugs, as his use of the exploit apparently violated the social network’s Terms of Service (ToS). In an August 19 posting on Hacker News, a Facebook security team member suggested that the bug had been fixed late last week. “We get hundreds of reports every day,” this person wrote. “Many of our best reports come from people whose English isn't great—though this can be challenging, it's something we work with just fine and we have paid out over $1 million to hundreds of reporters.” Because Shreateh used the bug to exploit real users without their consent, the team member continued, he violated the ToS and is thus ineligible for payment: “We welcome and will pay out for future reports from him (and anyone else!) if they're found and demonstrated within these guidelines.” Let that be a lesson to any white-hat hackers out there: targeting Mark Zuckerberg will get Facebook’s attention, but probably not in the way you originally intended. Image: Khalil Shreateh
Zuckerberg's Facebook wall, hacked.[/caption] Pop quiz for any security researchers out there: What’s the best way to draw Facebook’s attention to a bug that allows users to post messages on strangers’ walls? If you’re self-described security researcher Khalil Shreateh, the answer is: “Post a message about it on Mark Zuckerberg’s Facebook wall.” Shreateh doesn’t know Zuckerberg, but he used the bug to announce his findings right on the Facebook CEO’s timeline. Facebook, of course, reacted to Shreateh’s little stunt by disabling his account; minutes later, a company security engineer reached out to him, demanding the inner workings of the exploit. Which is funny, because Shreateh had already reached out to Facebook’s security team about the issue, via the Facebook Whitehat URL. When that didn’t work (“I don’t see anything when I click on the link except an error,” a Facebook security employee wrote back, according to Shreateh’s Website), he used the exploit to post a message onto the Facebook page of Sarah Goodin, a friend of Zuckerberg’s and one of the first people to create an account on the social network in Ye Olden Days. “Facebook security replay was that the link gives error opening,” Shreateh wrote on his blog, referring to the Facebook security employee’s earlier email. “If course they didnt use their authority to view sarah's privacy posts as sarah share her timeline posts with her friends only, i was able to view that post cause i'am the one who did post it even i'am not in her friend list.” After Facebook security refused to listen to him again (“I am sorry, this is not a bug,” they wrote back), Shreateh felt he had “no choice” but to post directly to Zuckerberg’s timeline. The response to that, of course, was immediate. “Unfortunately your report to our Whitehat system did not have enough technical information for us to take action on it,” Facebook reportedly wrote to him. “We cannot respond to reports which do not contain enough detail to allow us to reproduce an issue.” Facebook also refused to pay him the customary fee awarded to those who discover system bugs, as his use of the exploit apparently violated the social network’s Terms of Service (ToS). In an August 19 posting on Hacker News, a Facebook security team member suggested that the bug had been fixed late last week. “We get hundreds of reports every day,” this person wrote. “Many of our best reports come from people whose English isn't great—though this can be challenging, it's something we work with just fine and we have paid out over $1 million to hundreds of reporters.” Because Shreateh used the bug to exploit real users without their consent, the team member continued, he violated the ToS and is thus ineligible for payment: “We welcome and will pay out for future reports from him (and anyone else!) if they're found and demonstrated within these guidelines.” Let that be a lesson to any white-hat hackers out there: targeting Mark Zuckerberg will get Facebook’s attention, but probably not in the way you originally intended. Image: Khalil Shreateh