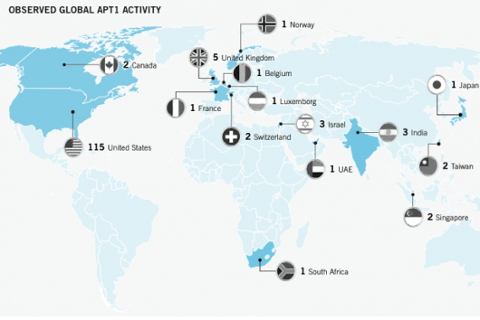
Chinese hackers have managed to infiltrate a number of advanced United States weapons systems, according to a confidential Pentagon report viewed by The Washington Post. Those infiltrated systems include programs “critical to U.S. missile defenses and combat aircraft and ships,” according to the newspaper. The report, prepared by the Defense Science Board, lists the ultra-expensive F-35 Joint Strike Fighter, the Navy’s Aegis ballistic-missile defense system, and the V-22 Osprey among the compromised systems. But the report “did not accuse the Chinese of stealing the designs,” the Post added. In theory, China (or any other country) could use those designs to accelerate their own weapons programs, or discover vulnerabilities exploitable in future combat. U.S. officials have indicated that the Pentagon’s extensive network of defense contractors is routinely targeted by cyber-attackers, who can exploit any number of weaknesses to gain access to sensitive data. While the Pentagon has launched programs to beef up its cyber-security, the extent of the current systems infiltration suggests that such efforts have a long way to go. Back in February, a report from cyber-security firm Mandiant drew connections between a prolific hacker group and the Chinese military. “Mandiant continues to track dozens of APT [Advanced Persistent Threat] groups around the world; however, this report is focused on the most prolific of these groups,” read the report’s executive summary. “We refer to this group as ‘APT1’ and it is one of more than 20 APT groups with origins in China.” The report claimed that APT1, which has been operating since at least 2006, “is believed to be the 2nd Bureau of the People’s Liberation Army (PLA) General Staff Department’s (GSD) 3rd Department,” also known as Unit 61398. Unit 61398 is located in a 12-story building on Datong Road in Gaoqiaozhen, in the Pudong New Area of Shanghai. Mandiant estimated that the Unit is staffed “by hundreds, and perhaps thousands of people,” many of them trained in computer security and network operations. Given the volume and type of attack activity, the organization’s main operators would require extensive support from linguists, open-source researchers, and IT experts. Mandiant’s report was highlighted by The New York Times, which offered a preview a day before publication. In late January, the Times alleged that its systems had been penetrated by Chinese hackers, who broke into e-mail accounts of reporters investigating the family of Chinese prime minister Wen Jiabao. (Mandiant had been hired by the Times to investigate that attack.) What do actual Chinese hackers think about their notoriety? In March, The Los Angeles Times released a report on a former Chinese military hacker who called himself “Rocy Bird” and described his job as a cyber-attacker in rather pedestrian terms. How can passionate young people like us handle a prison-like environment like this?” he ranted in one of many blog entries. But for the U.S. government, his work—and that of thousands of other Chinese hackers—is anything but dull. Image: TsuneoMP/Shutterstock.com
Chinese hackers have managed to infiltrate a number of advanced United States weapons systems, according to a confidential Pentagon report viewed by The Washington Post. Those infiltrated systems include programs “critical to U.S. missile defenses and combat aircraft and ships,” according to the newspaper. The report, prepared by the Defense Science Board, lists the ultra-expensive F-35 Joint Strike Fighter, the Navy’s Aegis ballistic-missile defense system, and the V-22 Osprey among the compromised systems. But the report “did not accuse the Chinese of stealing the designs,” the Post added. In theory, China (or any other country) could use those designs to accelerate their own weapons programs, or discover vulnerabilities exploitable in future combat. U.S. officials have indicated that the Pentagon’s extensive network of defense contractors is routinely targeted by cyber-attackers, who can exploit any number of weaknesses to gain access to sensitive data. While the Pentagon has launched programs to beef up its cyber-security, the extent of the current systems infiltration suggests that such efforts have a long way to go. Back in February, a report from cyber-security firm Mandiant drew connections between a prolific hacker group and the Chinese military. “Mandiant continues to track dozens of APT [Advanced Persistent Threat] groups around the world; however, this report is focused on the most prolific of these groups,” read the report’s executive summary. “We refer to this group as ‘APT1’ and it is one of more than 20 APT groups with origins in China.” The report claimed that APT1, which has been operating since at least 2006, “is believed to be the 2nd Bureau of the People’s Liberation Army (PLA) General Staff Department’s (GSD) 3rd Department,” also known as Unit 61398. Unit 61398 is located in a 12-story building on Datong Road in Gaoqiaozhen, in the Pudong New Area of Shanghai. Mandiant estimated that the Unit is staffed “by hundreds, and perhaps thousands of people,” many of them trained in computer security and network operations. Given the volume and type of attack activity, the organization’s main operators would require extensive support from linguists, open-source researchers, and IT experts. Mandiant’s report was highlighted by The New York Times, which offered a preview a day before publication. In late January, the Times alleged that its systems had been penetrated by Chinese hackers, who broke into e-mail accounts of reporters investigating the family of Chinese prime minister Wen Jiabao. (Mandiant had been hired by the Times to investigate that attack.) What do actual Chinese hackers think about their notoriety? In March, The Los Angeles Times released a report on a former Chinese military hacker who called himself “Rocy Bird” and described his job as a cyber-attacker in rather pedestrian terms. How can passionate young people like us handle a prison-like environment like this?” he ranted in one of many blog entries. But for the U.S. government, his work—and that of thousands of other Chinese hackers—is anything but dull. Image: TsuneoMP/Shutterstock.com Chinese Hackers Infiltrated Advanced U.S. Weapons Systems: Report
 Chinese hackers have managed to infiltrate a number of advanced United States weapons systems, according to a confidential Pentagon report viewed by The Washington Post. Those infiltrated systems include programs “critical to U.S. missile defenses and combat aircraft and ships,” according to the newspaper. The report, prepared by the Defense Science Board, lists the ultra-expensive F-35 Joint Strike Fighter, the Navy’s Aegis ballistic-missile defense system, and the V-22 Osprey among the compromised systems. But the report “did not accuse the Chinese of stealing the designs,” the Post added. In theory, China (or any other country) could use those designs to accelerate their own weapons programs, or discover vulnerabilities exploitable in future combat. U.S. officials have indicated that the Pentagon’s extensive network of defense contractors is routinely targeted by cyber-attackers, who can exploit any number of weaknesses to gain access to sensitive data. While the Pentagon has launched programs to beef up its cyber-security, the extent of the current systems infiltration suggests that such efforts have a long way to go. Back in February, a report from cyber-security firm Mandiant drew connections between a prolific hacker group and the Chinese military. “Mandiant continues to track dozens of APT [Advanced Persistent Threat] groups around the world; however, this report is focused on the most prolific of these groups,” read the report’s executive summary. “We refer to this group as ‘APT1’ and it is one of more than 20 APT groups with origins in China.” The report claimed that APT1, which has been operating since at least 2006, “is believed to be the 2nd Bureau of the People’s Liberation Army (PLA) General Staff Department’s (GSD) 3rd Department,” also known as Unit 61398. Unit 61398 is located in a 12-story building on Datong Road in Gaoqiaozhen, in the Pudong New Area of Shanghai. Mandiant estimated that the Unit is staffed “by hundreds, and perhaps thousands of people,” many of them trained in computer security and network operations. Given the volume and type of attack activity, the organization’s main operators would require extensive support from linguists, open-source researchers, and IT experts. Mandiant’s report was highlighted by The New York Times, which offered a preview a day before publication. In late January, the Times alleged that its systems had been penetrated by Chinese hackers, who broke into e-mail accounts of reporters investigating the family of Chinese prime minister Wen Jiabao. (Mandiant had been hired by the Times to investigate that attack.) What do actual Chinese hackers think about their notoriety? In March, The Los Angeles Times released a report on a former Chinese military hacker who called himself “Rocy Bird” and described his job as a cyber-attacker in rather pedestrian terms. How can passionate young people like us handle a prison-like environment like this?” he ranted in one of many blog entries. But for the U.S. government, his work—and that of thousands of other Chinese hackers—is anything but dull. Image: TsuneoMP/Shutterstock.com
Chinese hackers have managed to infiltrate a number of advanced United States weapons systems, according to a confidential Pentagon report viewed by The Washington Post. Those infiltrated systems include programs “critical to U.S. missile defenses and combat aircraft and ships,” according to the newspaper. The report, prepared by the Defense Science Board, lists the ultra-expensive F-35 Joint Strike Fighter, the Navy’s Aegis ballistic-missile defense system, and the V-22 Osprey among the compromised systems. But the report “did not accuse the Chinese of stealing the designs,” the Post added. In theory, China (or any other country) could use those designs to accelerate their own weapons programs, or discover vulnerabilities exploitable in future combat. U.S. officials have indicated that the Pentagon’s extensive network of defense contractors is routinely targeted by cyber-attackers, who can exploit any number of weaknesses to gain access to sensitive data. While the Pentagon has launched programs to beef up its cyber-security, the extent of the current systems infiltration suggests that such efforts have a long way to go. Back in February, a report from cyber-security firm Mandiant drew connections between a prolific hacker group and the Chinese military. “Mandiant continues to track dozens of APT [Advanced Persistent Threat] groups around the world; however, this report is focused on the most prolific of these groups,” read the report’s executive summary. “We refer to this group as ‘APT1’ and it is one of more than 20 APT groups with origins in China.” The report claimed that APT1, which has been operating since at least 2006, “is believed to be the 2nd Bureau of the People’s Liberation Army (PLA) General Staff Department’s (GSD) 3rd Department,” also known as Unit 61398. Unit 61398 is located in a 12-story building on Datong Road in Gaoqiaozhen, in the Pudong New Area of Shanghai. Mandiant estimated that the Unit is staffed “by hundreds, and perhaps thousands of people,” many of them trained in computer security and network operations. Given the volume and type of attack activity, the organization’s main operators would require extensive support from linguists, open-source researchers, and IT experts. Mandiant’s report was highlighted by The New York Times, which offered a preview a day before publication. In late January, the Times alleged that its systems had been penetrated by Chinese hackers, who broke into e-mail accounts of reporters investigating the family of Chinese prime minister Wen Jiabao. (Mandiant had been hired by the Times to investigate that attack.) What do actual Chinese hackers think about their notoriety? In March, The Los Angeles Times released a report on a former Chinese military hacker who called himself “Rocy Bird” and described his job as a cyber-attacker in rather pedestrian terms. How can passionate young people like us handle a prison-like environment like this?” he ranted in one of many blog entries. But for the U.S. government, his work—and that of thousands of other Chinese hackers—is anything but dull. Image: TsuneoMP/Shutterstock.com