Some Amazon S3 Buckets Exposed to Public Scrutiny: Rapid 7
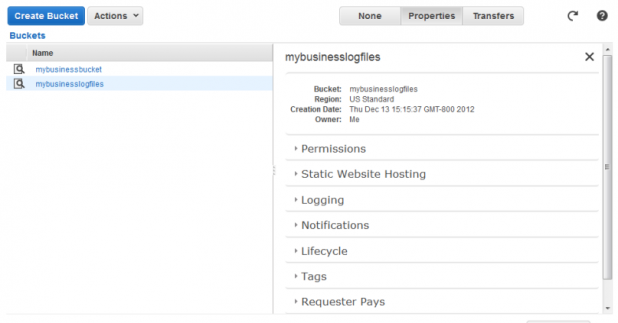
According to IT security firm Rapid 7, there are a couple of holes in Amazon’s buckets. No, not physical buckets, like the plastic ones you buy from the online retailer for an outdoor project: the virtual buckets that Amazon’s Simple Storage Service (S3) uses to organize files. Amazon Web Services (AWS) users can access these buckets via a particular URL, after setting access controls for the buckets and the objects contained within. The problem is that a lot of AWS users are leaving their buckets public, exposing potentially sensitive information to anyone cruising the Web. “The worst case scenario is that a bucket has been marked as ‘public,’ exposes a list of sensitive files, and no access controls have been placed on those files,” read the March 27 note on Rapid 7’s blog. “In situations where the bucket is public, but the files are locked down, sensitive information can still be exposed through the file names themselves, such as the names of customers or how frequently a particular application is backed up.” (Hat tip to InfoWorld for discovering the posting.) A public bucket isn’t Amazon’s fault, the posting added, “but rather a misconfiguration caused by the owner of the bucket.” However, it’s an oversight with potentially massive consequences: Rapid 7 managed to generate a list of 126 billion files from 1,951 public buckets, and reviewed a random sample of 40,000 publicly visible files stuffed with sensitive data, including employee information, PHP source code, video-game development tools, sales records, and personal photos from “a medium-sized social media service.” In order to assemble a list of valid bucket names, Rapid 7 relied on a number of different tactics: querying the Bing Search API, extracting S3 links from HTTP responses identified by the Critical.IO project, and brute guessing (such as matching Fortune 1000 company names “with permutations on .com, -backup, -media.”) Invalid buckets returned a “NoSuchBucket” error, allowing the firm to narrow down the list in a definitive way. A bad actor with that sensitive data could launch all sorts of hilarious evil, including network attacks, or merely sell it to the highest bidder. Even if users have the files in their public buckets “locked down,” as it were, an intruder could still get a good look at the filenames, which could expose client or sales information. “Check if you own one of the open buckets and if so, think about what you're keeping in that buckets and whether you really want it exposed to the internet and anyone curious to take a look,” the posting concluded. “If you don't, remediation is quite simple for this one, and Amazon has made it even easier by helpfully walking through the options for you.” Amazon’s AWS security is apparently working to put some sort of measures in place to identify misconfigured files and buckets. Whether the company makes some public announcement about those efforts remains to be seen. Image: Amazon