Hacker Group Connected to Chinese Military: Mandiant Report
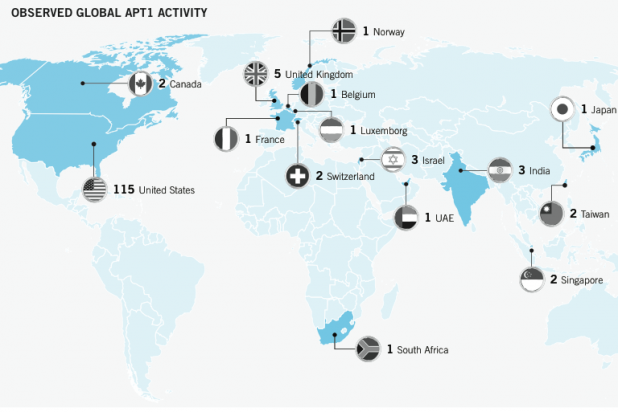
A new report from cyber-security firm Mandiant draws connections between a prolific hacker group and the Chinese military. “Mandiant continues to track dozens of APT [Advanced Persistent Threat] groups around the world; however, this report is focused on the most prolific of these groups,” reads the report’s executive summary. “We refer to this group as ‘APT1’ and it is one of more than 20 APT groups with origins in China.” The report claims that APT1, which has been operating since at least 2006, “is believed to be the 2nd Bureau of the People’s Liberation Army (PLA) General Staff Department’s (GSD) 3rd Department,” also known as Unit 61398. Unit 61398 is located in a 12-story building on Datong Road in Gaoqiaozhen, in the Pudong New Area of Shanghai. Mandiant estimates that the Unit is staffed “by hundreds, and perhaps thousands of people,” many of them trained in computer security and network operations. Given the volume and type of attack activity, the organization’s main operators would require extensive support from linguists, open-source researchers, and IT experts. “Since 2006, Mandiant has observed APT1 compromise 141 companies spanning 20 major industries,” the report continues. “APT1 has a well-defined attack methodology, honed over years and designed to steal large volumes of valuable intellectual property.” APT1 has the ability to access victim networks for an average of 356 days, stealing terabytes of compressed data during that period. Information stolen by the group includes manufacturing procedures, business plans, policy positions and analysis, emails of high-ranking employees, user credentials, and product development and use. However, Mandiant lacks “direct evidence” about who ends up receiving that information, or how all that data is processed into a usable form. APT1 relies on “spear phishing” as a primary route of attack, shooting out fake emails that, when clicked by an unsuspecting recipient, create a custom backdoor into the network. With that foothold established, APT1 can then reconnoiter a network, install new backdoors, and log into various Web portals. From there, it’s a relatively simple process to spirit away any files of interest. “We believe the totality of the evidence we provide in this document bolsters the claim that APT1 is Unit 61398,” the report concludes, while leaving the door propped open to another “unlikely” possibility: that a shadow organization full of Chinese speakers with access to Shanghai-based telecommunications infrastructure is running a full-scale cyber-espionage campaign “right outside of Unit 61398’s gates, performing tasks similar to Unit 61398’s known mission.” Mandiant realizes that publishing the report, with the attendant publicity, could drive hackers to change their techniques—which could lessen the ability to track them with accuracy. “It is our sincere hope, however, that this report can temporarily increase the costs of Unit 61398’s operations and impede their progress in a meaningful way,” the report concludes. “We are acutely aware of the risk this report poses for us. We expect reprisals from China as well as an onslaught of criticism.” Mandiant’s report received a generous burst of publicity from The New York Times, which offered a preview a day before publication. In late January, the Times alleged that its systems had been penetrated by Chinese hackers, who broke into e-mail accounts of reporters investigating the family of Chinese prime minister Wen Jiabao. (Mandiant had been hired by the Times to investigate that attack.) “Attackers no longer go after our firewall,” Michael Higgins, the Times chief security officer, told reporters from his newspaper. “They go after individuals. They send a malicious piece of code to your e-mail account and you’re opening it and letting them in.” Image: Mandiant