The Hunt for Red October
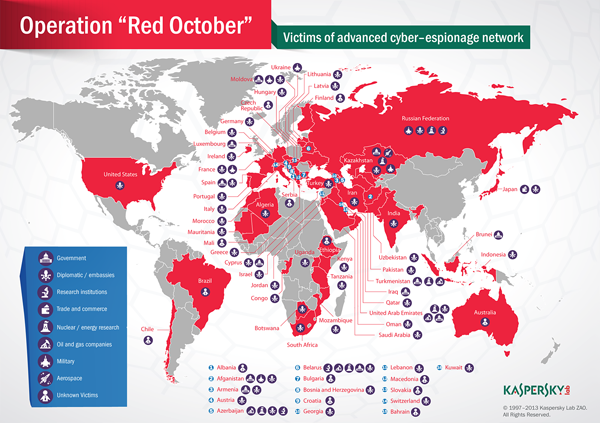
Kaspersky Lab researchers claim to have uncovered what they describe as a “high-level cyber-espionage campaign” that has infiltrated networks at diplomatic, governmental and scientific research organizations over the past five years. Dubbed “Red October,” the campaign involves the use of malware to siphon data from mobile devices, PCs, and network hardware. Targeted countries include the United States, Brazil, Australia, Russia, and a host of others from North America to Eastern Europe and Africa. Multiple command-and-control servers are still pulling in stolen data. “The attackers created a multi-functional framework which is capable of applying quick extension of the features that gather intelligence,” read Kaspersky Lab’s posting on the matter. “The system is resistant to C&C server takeover and allows the attacker to recover access to infected machines using alternative communication channels.” Researchers observed the use of three different exploits for known vulnerabilities, including ones in Microsoft Excel (CVE-2009-3129) and Word (CVE-2010-3333 and CVE-2012-0158). “The earliest known attacks used the exploit for MS Excel and took place in 2010 and 2011,” the posting added, “while attacks targeting the MS Word vulnerabilities appeared in the summer of 2012.” Once within the target network, the attackers “deploy a module to actively scan the local area network, find hosts vulnerable for MS08-067 (the vulnerability exploited by Conficker) or accessible with admin credentials from its own password database.” Another module leverages that information to infect remote hosts on the same network. Kaspersky Lab researchers found mobile modules capable of stealing information from Windows Mobile, iPhone, and Nokia devices; in all, it uncovered more than 1,000 modules linked to 30 different module categories. Kaspersky Lab believes the attackers have “Russian-speaking origins,” based on registration data of the command-and-control servers and various artifacts left in malware executables. While Russian-speaking operatives created the malware modules, it believes that Chinese hackers were responsible for the actual exploits. The organization found no evidence linking the activity with any sort of nation-state sponsored attack, although the information stolen could easily be sold to the highest-bidding nation-states. “The main purpose of the operation appears to be the gathering of classified information and geopolitical intelligence, although it seems that the information gathering scope is quite wide,” the posting read. “During the past five years, the attackers collected information from hundreds of high profile victims although it's unknown how the information was used.” Image: Kaspersky Lab