[caption id="attachment_13937" align="aligncenter" width="618"]
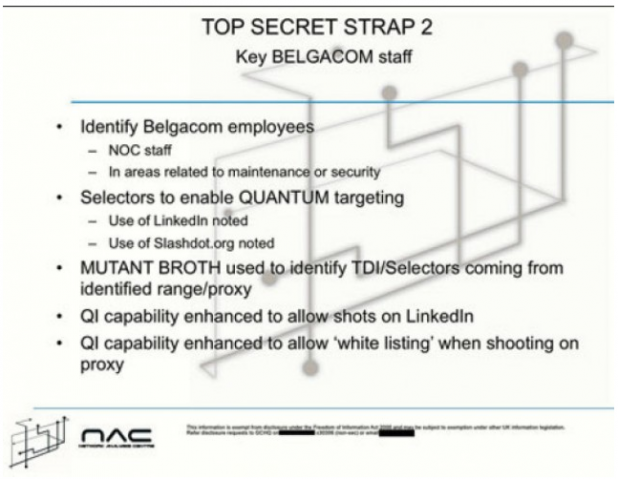
Purported slide showing how the GCHQ used fake LinkedIn and Slashdot Websites to infiltrate a Belgian telecommunications network.[/caption] The
GCHQ agency, Britain’s equivalent of the National Security Agency, reportedly used fake LinkedIn and Slashdot pages to load malware onto computers at Belgian telecommunications firm Belgacom. Government whistleblower Edward Snowden provided top-secret documents detailing the alleged hack to
German publication Der Spiegel. According to those documents, the GCHQ identified Belgacom employees who worked in network maintenance and security, and who spent significant amounts of time on LinkedIn and Slashdot. With that information, the agency initiated a “quantum insert,” which directed those targeted employees to fake, malware-rich versions of those two Websites. That malware reportedly gave the GCHQ access to Belgacom’s internal network, from which it siphoned information related to OPEC and other matters of international importance. In an emailed statement to Slashdot, the GCHQ’s Press and Media Affairs Office wrote: “We have no comment to make on this particular story.” It added:
“All GCHQ's work is carried out in accordance with a strict legal and policy framework which ensure that our activities are authorised, necessary and proportionate, and that there is rigorous oversight, including from the Secretary of State, the Interception and Intelligence Services Commissioners and the Intelligence and Security Committee.”
Meanwhile, LinkedIn’s representatives suggested they had no knowledge of the reported hack. “We have read the same stories, and we want to clarify that we have never cooperated with any government agency,” a spokesperson from the social network wrote in an email to Slashdot, “nor do we have any knowledge, with regard to these actions, and to date, we have not detected any of the spoofing activity that is being reported.” That spokesperson also provided a link to LinkedIn’s
Transparency Report, which breaks down the requests it’s received from law enforcement and governments for user data. Jennifer Bewley, spokesperson for Dice Holdings, Inc. (which owns Slashdot), offered the following statement:
"We were alerted to these reported government agency actions by a submission on Slashdot made by the community Sunday evening linking to news stories. To be clear, we have not been asked to cooperate with any government agency related to this matter and have not provided access to Slashdot systems or user information. We know of no unauthorized Slashdot code manipulation, or attempts to effect any. We do not approve of this reported activity and if true, it's unfortunate that we are yet another in a long line of internet businesses to suffer this type of intrusion."
Slashdot and LinkedIn join a list of online businesses affected by alleged espionage by government agencies, including Google, Microsoft, Yahoo, Facebook, AOL, Skype, Apple, and YouTube. An IT security expert with extensive knowledge of government intelligence operations, but no direct insight into the GCHQ, hypothesized that carrying out a man-in-the-middle attack was well within the capabilities of British intelligence agencies, but that such a “retail” operation also seemed somewhat out of character. “Based on what we know they've done, they are doing industrialized, large scale traffic sweeping and net hacking,” he said. “They operate a wholesale, with statistical techniques. By ‘statistical’ I mean that they send something that may or may not work.” With that in mind, he added, it’s plausible that the GCHQ has software that operates in a similar manner to the NSA’s
EGOTISTICAL GIRAFFE, and used it to redirect Belgacom employees to a fake download. “However, the story has been slightly garbaged into it being fake [LinkedIn and Slashdot] accounts, as opposed to network spoofing.” In June, Snowden—also a former CIA employee—began feeding his documents to
The Guardian and other newspapers. Many of those documents suggested that the NSA, ordinarily tasked with intercepting communications from terrorists and foreign governments, collects massive amounts of information on ordinary Americans—which in turn ignited a firestorm of controversy. Those documents also included mentions of allied intelligence agencies such as GCHQ. Effectively exiled in Russia following those leaks, Snowden
now works in tech support. But journalists are continuing to use his information to uncover new aspects of the world’s surveillance culture.
Image: Der Spiegel 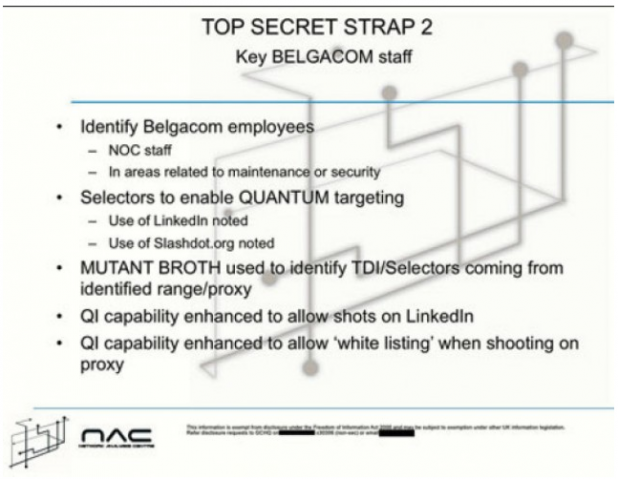 Purported slide showing how the GCHQ used fake LinkedIn and Slashdot Websites to infiltrate a Belgian telecommunications network.[/caption] The GCHQ agency, Britain’s equivalent of the National Security Agency, reportedly used fake LinkedIn and Slashdot pages to load malware onto computers at Belgian telecommunications firm Belgacom. Government whistleblower Edward Snowden provided top-secret documents detailing the alleged hack to German publication Der Spiegel. According to those documents, the GCHQ identified Belgacom employees who worked in network maintenance and security, and who spent significant amounts of time on LinkedIn and Slashdot. With that information, the agency initiated a “quantum insert,” which directed those targeted employees to fake, malware-rich versions of those two Websites. That malware reportedly gave the GCHQ access to Belgacom’s internal network, from which it siphoned information related to OPEC and other matters of international importance. In an emailed statement to Slashdot, the GCHQ’s Press and Media Affairs Office wrote: “We have no comment to make on this particular story.” It added:
Purported slide showing how the GCHQ used fake LinkedIn and Slashdot Websites to infiltrate a Belgian telecommunications network.[/caption] The GCHQ agency, Britain’s equivalent of the National Security Agency, reportedly used fake LinkedIn and Slashdot pages to load malware onto computers at Belgian telecommunications firm Belgacom. Government whistleblower Edward Snowden provided top-secret documents detailing the alleged hack to German publication Der Spiegel. According to those documents, the GCHQ identified Belgacom employees who worked in network maintenance and security, and who spent significant amounts of time on LinkedIn and Slashdot. With that information, the agency initiated a “quantum insert,” which directed those targeted employees to fake, malware-rich versions of those two Websites. That malware reportedly gave the GCHQ access to Belgacom’s internal network, from which it siphoned information related to OPEC and other matters of international importance. In an emailed statement to Slashdot, the GCHQ’s Press and Media Affairs Office wrote: “We have no comment to make on this particular story.” It added: